Apart from the usual bug fixes / new functionality, each Acunetix WVS update generally includes new vulnerability tests or an improvement to existing checks. In this post, I would like to summarize the new security tests added in the latest Acunetix WVS update.
Unicode Transformation Issues
This new security test is looking for issues that can occur when working with Unicode data. Specifically, it is looking for Best-Fit mappings, Overlong byte sequences and Ill-Formed Subsequences issues.
Best-Fit Mappings
occurs when a character X gets transformed to an entirely different character Y. For example, in some situations the Unicode character U+FF1C FULLWIDTH LESS-THAN SIGN can be transformed into U+003C LESS-THAN SIGN (<). This can cause serious security problems for the affected web application.
Overlong byte sequences
(non-shortest form) – UTF-8 allows for different representations of characters that also have a shorter form. For security reasons, a UTF-8 decoder must not accept UTF-8 sequences that are longer than necessary to encode a character. For example, the character U+000A (line feed) must be accepted from a UTF-8 stream only in the form 0x0A, but not in any of the following five possible overlong forms:
- 0xC0 0x8A
- 0xE0 0x80 0x8A
- 0xF0 0x80 0x80 0x8A
- 0xF8 0x80 0x80 0x80 0x8A
- 0xFC 0x80 0x80 0x80 0x80 0x8A
Ill-Formed Subsequences
– As REQUIRED by UNICODE 3.0, and noted in the Unicode Technical Report #36, the web application should not consume a leading byte when it is followed by an invalid successor byte. For example, at some point PHP was consuming the control characters leading to XSS and SQL injection vulnerabilities.
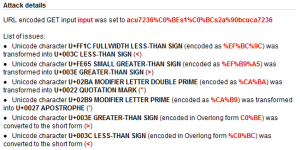
When testing a vulnerable web application, Acunetix WVS issues an Unicode Transformation Issues alert with the following details.
Here is a part of the HTTP request. As you can see the URL contains some Unicode characters. Specifically, it contains the Unicode character U+003E GREATER-THAN SIGN (encoded in Overlong form C0%BE).
In the HTTP response, this character was converted to the short form (>).
This is a security issue and can be used to bypass security filters.
Analyze Parameter Values
Another script introduced with this update is Analyze_Parameter_Values.script. This script is analyzing parameter values and performs various actions based on their values. For example, if the parameter value contains a filename or a file path, the script will pass this information to the crawler and these files will be crawled and tested in the next scan iteration.
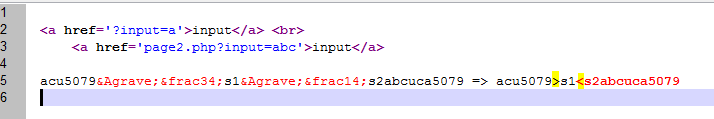
For example, the crawler generated this input scheme from one of our test web applications.
In this case, this input scheme contains a GET parameter named fname with 4 variations. Two of these variations are relative paths, one of them is a funny looking string and one is the string ‘bad’.
After enabling this script, the crawler produced the following results after the final iteration.
All the files/directories colored in light blue are files that are not linked directly and were discovered by this script.
It found a new file named SomeSecretFile.php, two new folders and two new files. As you can guess, SomeSecretFile.php and HiddenFolderAnotherSecretFile.php come from the input scheme variations but what’s with the HiddenFolder2ThirdSecretFile.php?
The script figured out that SGlkZGVuRm9sZGVyMi9UaGlyZFNlY3JldEZpbGUucGhw is encoded base64, decoded the value, understood that it looks like a file path and passed the information to the crawler. Sometimes, web applications are using base64 encoding to exchange filenames via parameter values and the script is looking for this behavior.
Also, these files have XSS vulnerabilities and the scanner found them in the final iteration.
Hidden Virtual Hosts
Finally, the latest update contains a script that is trying to find hidden Virtual Hosts on the tested web server. Virtual hosting is a method for hosting multiple domain names on a single web server.
Sometimes developers hosts internal/test applications on production systems without making them public. These virtual hosts are not directly accessible unless you guess the name of their virtual host, connect to the web server’s IP address and specify the virtual host in the Host header.
This script is looking for common Virtual Host names and compares the responses received with the normal response. When it finds differences, it will issue alerts for these names.
For example, here is an alert generated by this script.
In this case, a Virtual Host named svn has been identified. ‘svn’ is not directly accessible because it doesn’t have a FQDN (Fully qualified domain name). However, the scanner managed to access it by connecting to the IP address and requesting it via the Host header.
Get the latest content on web security
in your inbox each week.