Recently we’ve released a new build, build number 20091124. This build includes a new AcuSensor check named “curl_exec() url is controlled by user”. This new check will verify if the user can control the URL passed to curl_exec.
In case you are not familiar with curl, below is a short abstract about curl taken from PHP’s manual:
PHP supports libcurl, a library created by Daniel Stenberg, that allows you to connect and communicate to many different types of servers with many different types of protocols. libcurl currently supports the http, https, ftp, gopher, telnet, dict, file, and ldap protocols. libcurl also supports HTTPS certificates, HTTP POST, HTTP PUT, FTP uploading (this can also be done with PHP’s ftp extension), HTTP form based upload, proxies, cookies, and user+password authentication.
Usually, curl is used to connect and retrieve data from a remote URL using the http protocol. However, curl supports a bunch of protocols as you can see in the description above. One of these protocols is the file protocol. Using this protocol you can read local files by using an URL like file:///etc/passwd. Therefore, if the user can control the URL passed to curl_exec, in some cases (if the content is echoed back) it can read local files.
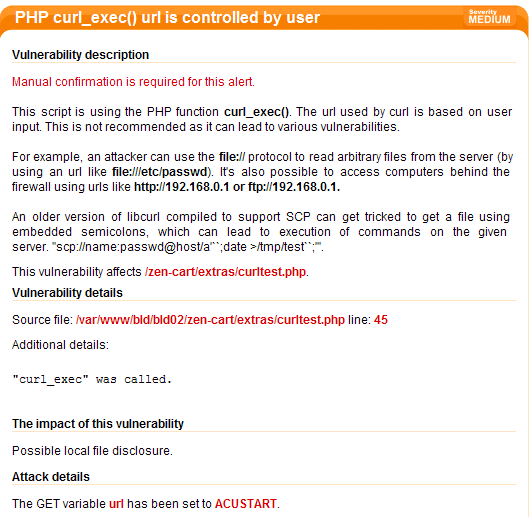
While testing this new AcuSensor check on different applications, I’ve found a real-life example of a vulnerable application. I’m talking about Zen Cart. Acunetix WVS issued the following alert:
From Wikipedia:
Zen Cart is an open source online store management system. It is PHP-based, using a MySQL database and HTML components. Support is provided for several languages and currencies, and it is freely available under the GNU General Public License.
Zen Cart contains a directory named extras where there are different test scripts. One of these scripts is curltest.php. This script is used for testing is the curl PHP library is installed and is working properly.
The source code of this script looks like this (only relevant pieces of code are shown):
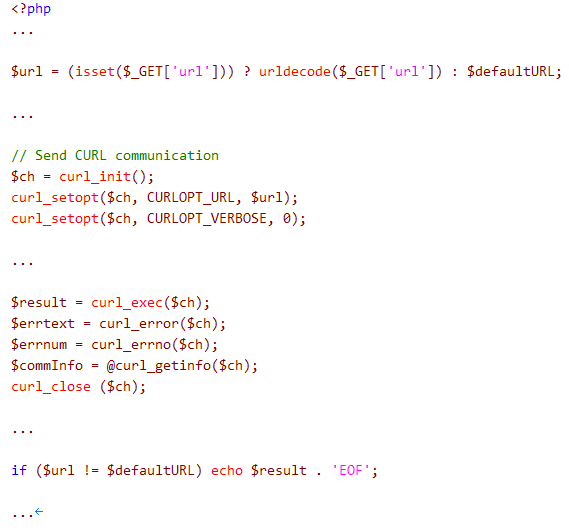
As you can see above, the URL passed to the curl_setopt (CURLOPT_URL) function and later used by curl_exec comes from user input ($_GET[‘url’]).
Also, the file contents (saved in the $result) are echoed back to the user. Therefore we cane read the contents of any file from the remote server.

As you can see in the screenshot above, it’s possible to read the contents of the /etc/passwd file.
However, the extras directory contains other test scripts. One of them, named ipn_test_return.php, is not properly written and will display an error message when called directly:
If you issue a request like http://bld02:80/zen-cart/extras/ipn_test_return.php
you will receive the following error message:
<br />
<b>Fatal error</b>: require() [<a href=’function.require’>function.require</a>]: Failed opening required ‘includes/application_top.php’ (include_path=’.:/usr/share/php:/usr/share/pear’) in <b>/var/www/bld/bld02/zen-cart/extras/ipn_test_return.php</b> on line <b>14</b><br />
This error message reveals the local path, so now we know where the application is installed. This could be useful to read the contents of the configuration file (includes/configure.php). This file contains the database credentials. If the Zen Cart database is not stored on the local server, it’s possible to access the database remotely.
Also, even without the file:// protocol, it’s possible to access hosts behind the firewall by issuing requests like
http://bld02/zen-cart/extras/curltest.php?url=http://192.168.0.1 or
http://bld02/zen-cart/extras/curltest.php?url=http://192.168.1.1.
The vendor released a security alert after being notified by us. They advise users to completely remove the extras directory as it’s not required by Zen Cart and it was distributed only for troubleshooting.
The security alert can be found here.
Get the latest content on web security
in your inbox each week.




