A security research team called Vulnerability-Lab have discovered a persistent XSS vulnerability in the official website of Barack Obama. This is not the first time that the president’s website was targeted. About a year ago SecurityShell reported a similar XSS vulnerability on their blog.
This time the president was lucky; the hackers were ethical and reported the exploit before publicly disclosing it. The Barack Obama website administrators took over a week to respond, but eventually patched their system with some help from the researchers. This is the white hat world where hackers follow a procedure called Responsible Disclosure. They report the exploit to the web site and wait for a fix before announcing their discovery. However there is also a dark side – an underworld of cyber-criminals who exploit website vulnerabilities for financial or political gain.
Below is the original report timeline, at the time of writing I did not have a confirmed date of the Patch, however the researchers told me that the website is not vulnerable anymore.
Report-Timeline:
================
2011-08-30: Vendor Notification
2011-09-19: Vendor Response/Feedback
2011-09-**: Vendor Fix/Patch
2011-09-12: Public or Non-Public Disclosure

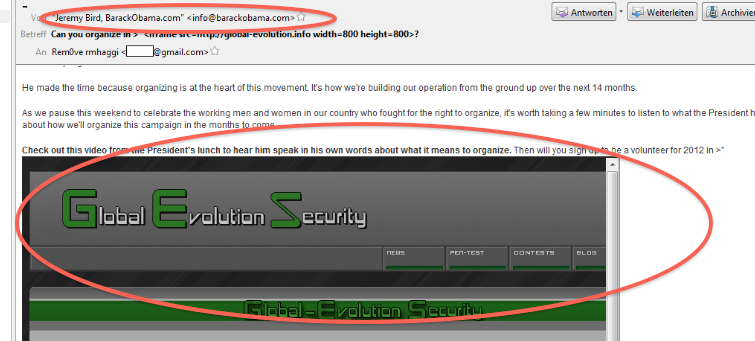
Image from last year’s hack against the same website
Many times XSS vulnerabilities are used to deface websites. This type of activity is the equivalent of throwing paint on a billboard on the highway. It’s easy to do and ugly for the website, however the damage is easily reversed.
This particular exploit appears to be more sophisticated than simple vandalism. Vulnerability-Lab succeeded in injecting Javascript into the back-end of the website. This Javascript, made it all the way into mailshots generated by the system. In their Proof of Concept (PoC) code the researchers demonstrated how an IFRAME exploit could be inserted into emails sent from info@barackobama.com.
The screenshot above shows a page from the Global Evolution Security website as it appears embedded in an email sent from the barackobama.com website. The email source is below:
Check out this video from the President’s lunch to hear him speak=20
in his own words about what it means to organize. Then will you=20
sign up to be a volunteer for 2012 in >”<iframe =
src=3Dhttp://vulnerability-lab.com width=3D800 height=3D800>?
The attackers managed to inject this by exploiting a vulnerability in the volunteer signup form that is available on the website.
During the signup process, the user is asked for his name, email address and other details. This form allowed them to inject the script tags that made the attack possible. Apart from appearing in emails, the attack script also appeared on other parts of the website, meaning that visitors to the barackobama.com web page were also vulnerable.
XSS attacks are often overshadowed by their ugly cousin – SQL Injection. This causes them to remain undetected for a long time. SQL Injection attacks do a lot of damage and are much more frequent, however here we see once again that XSS can be used effectively with devastating effects.
To circumvent these types of attacks it is important to run automated vulnerability scans using a Web Vulnerability Scanner. Vulnerability scanning should be followed by thorough code reviews and patches must be applied where necessary.
Get the latest content on web security
in your inbox each week.