Acunetix version 12 (build 12.0.190927120) has been released.
This new build introduces a number of updates including ad-blocking in the scanner resulting in faster scans, support for Session HTTP headers, the ability to run scans for vulnerabilities introduced in the latest Acunetix update, and the ability to configure internal Acunetix settings. This new build includes vulnerability checks for SAP Commerce Cloud, Yii2, Mojolicious, and Webmin together with a number of updates and fixes, all of which are available for Acunetix on-premise for Windows and Linux and Acunetix Online.
Here is a full set of updates:
New Features
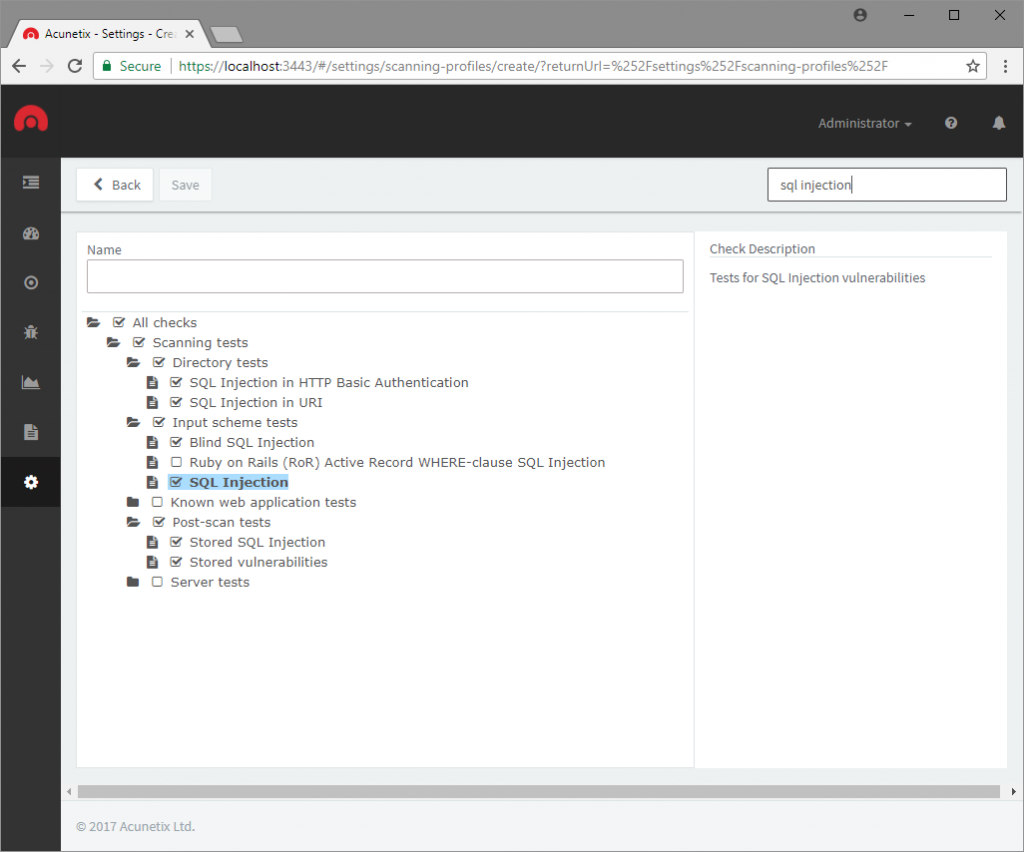
- Introduced new Scan Type: New Web Vulnerabilities to scan for new vulnerabilities introduced in the latest Acunetix update
- Introduced ad-blocking in the scanner, resulting in faster scans
- Implemented support for Session HTTP headers when logging in to the site
- Introduced custom_settings.xml to configure settings from settings.xml, which are not overwritten on upgrade
New Vulnerability Checks
- New test for insecure Java deserialization causing RCE in SAP Commerce Cloud (CVE-2019-0344)
- New test for a weak key used to sign a cookie in Yii2
- New test for a weak key used to sign a cookie in Mojolicious
- New test for Webmin 0day remote code execution (CVE-2019-15107)
- Updated WordPress Core and WordPress Plugin vulnerability checks
Updates
- The scan will now report when an invalid Selenium script is used as an import file
- Improved detection of the type of Burp import file being used
- Increased limit on Custom Headers
- Multiple improvements in DeepScan
- The LSR Record button is disabled during Login Action playback
- Acunetix will start reporting login forms when no login credentials are configured
- The tester user will not be able to create or view reports
Fixes
- Fixed: Directory Traversal vulnerabilities were sometimes incorrectly reported as found with AcuSensor
- Fixed: Several broken references in the vulnerability alerts
- Fixed: HTTP Response was not shown in some vulnerability alerts
- Fixed an issue causing DeepScan to take too long to process some locations
- Fix in PHP Hash Collision DOS vulnerability check
- Fixed: Integrated LSR was not working on IE11
- Fixed: Selenium script playback fails for some scripts
- Fixed: Session Detection fails if session pattern spans multiple lines
- Fixed: LSR keeps showing the spinner on some pages
- Fixed: LSR Session pattern was not always saved when detected using the navigation
- Fixed: LSR Session pattern check might fail for in body / not in body patterns
- Fixed: On some systems, Chromium processes cannot be terminated when generating PDF reports
- Fixed: Passwords were recoverable from the UI
- Better handling of HTTP timeouts by vulnerability checks
Upgrade to the latest build
If you are already using Acunetix v12, you can initiate the automatic upgrade from the new build notification in the Acunetix UI > Settings page.
If you are using a previous version of Acunetix, you need to download Acunetix version 12 from here. Use your Acunetix License Key to download and activate your product.
Get the latest content on web security
in your inbox each week.