Cross Site Request Forgery. Keep protected with a CSRF Scanner
Cross-site Request Forgery (CSRF), XSRF, or Sea surf vulnerabilities are common web application security vulnerabilities found in many off-the-shelf, open-source, and custom-built web applications. A CSRF attack involves an attacker leveraging a web application vulnerability to trick an unsuspecting victim (usually via social engineering) into making an authenticated request that the victim did not intend to make.
In a CSRF attack, the victim’s web browser cannot distinguish between a legitimate and a malicious request and is therefore tricked into executing unwanted actions to the web application as intended by the attacker. When sending an HTTP request to a website that the user is already logged in to, the browser will dutifully send the session cookie (containing the user’s session ID) to the web server. Unfortunately, this is precisely what the attacker is after – to “forge” requests on behalf of the end-user. Since a vulnerable application would not use any anti-CSRF tokens, the application will accept the forged request and carry out the attacker’s bidding.
A typical CSRF would involve submitting forms present on the web application to alter data. An example of this would be for an attacker to reset an administrator’s password. Therefore, a CSRF vulnerability affecting highly privileged users, such as administrators, could result in full application compromise.
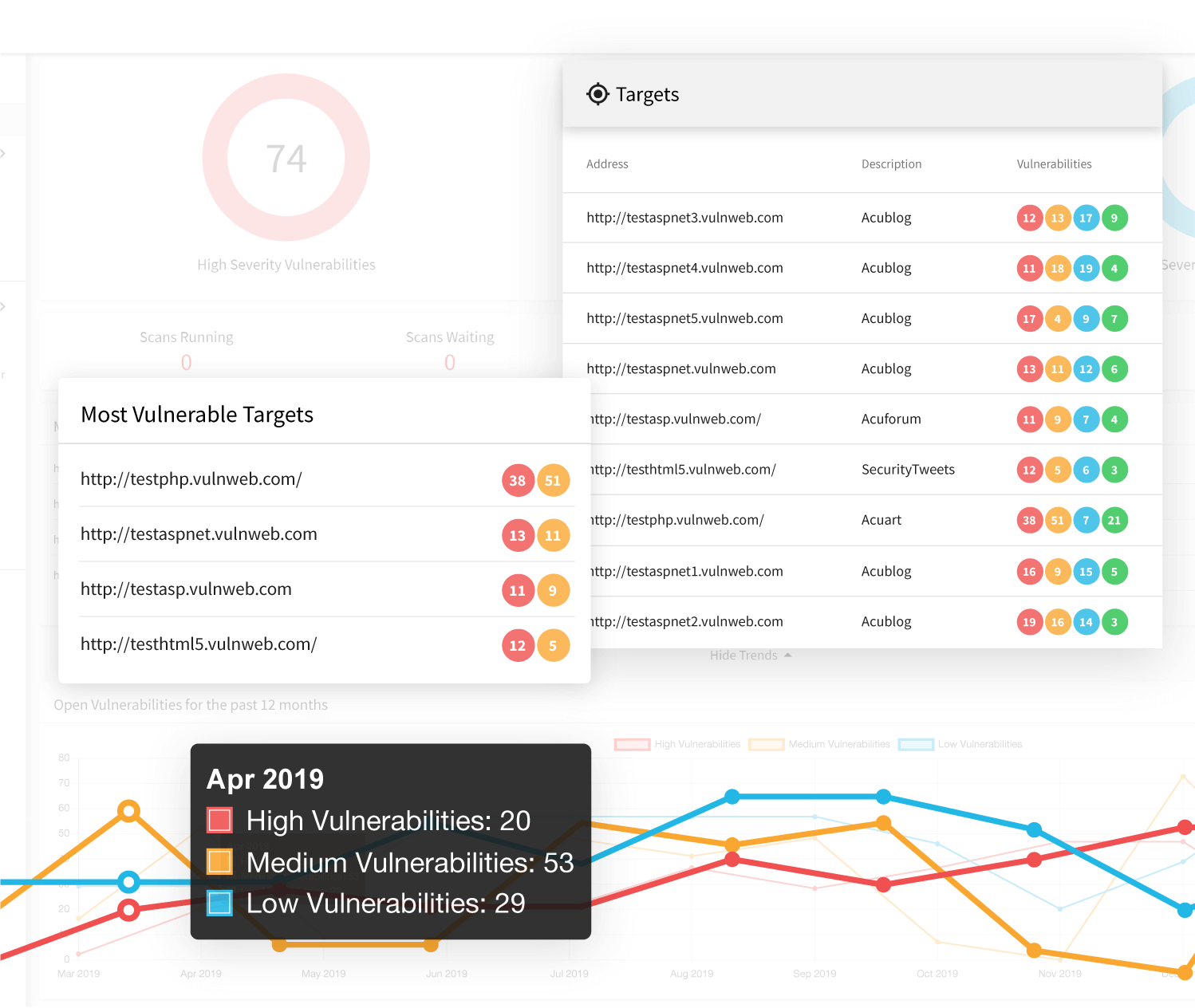
CSRF vulnerabilities could be challenging without the right tools. Acunetix is a website security scanner and the myriad of vulnerability test that it performs includes Cross-site Request Forgery (CSRF).
Beyond Low-Hanging Fruit
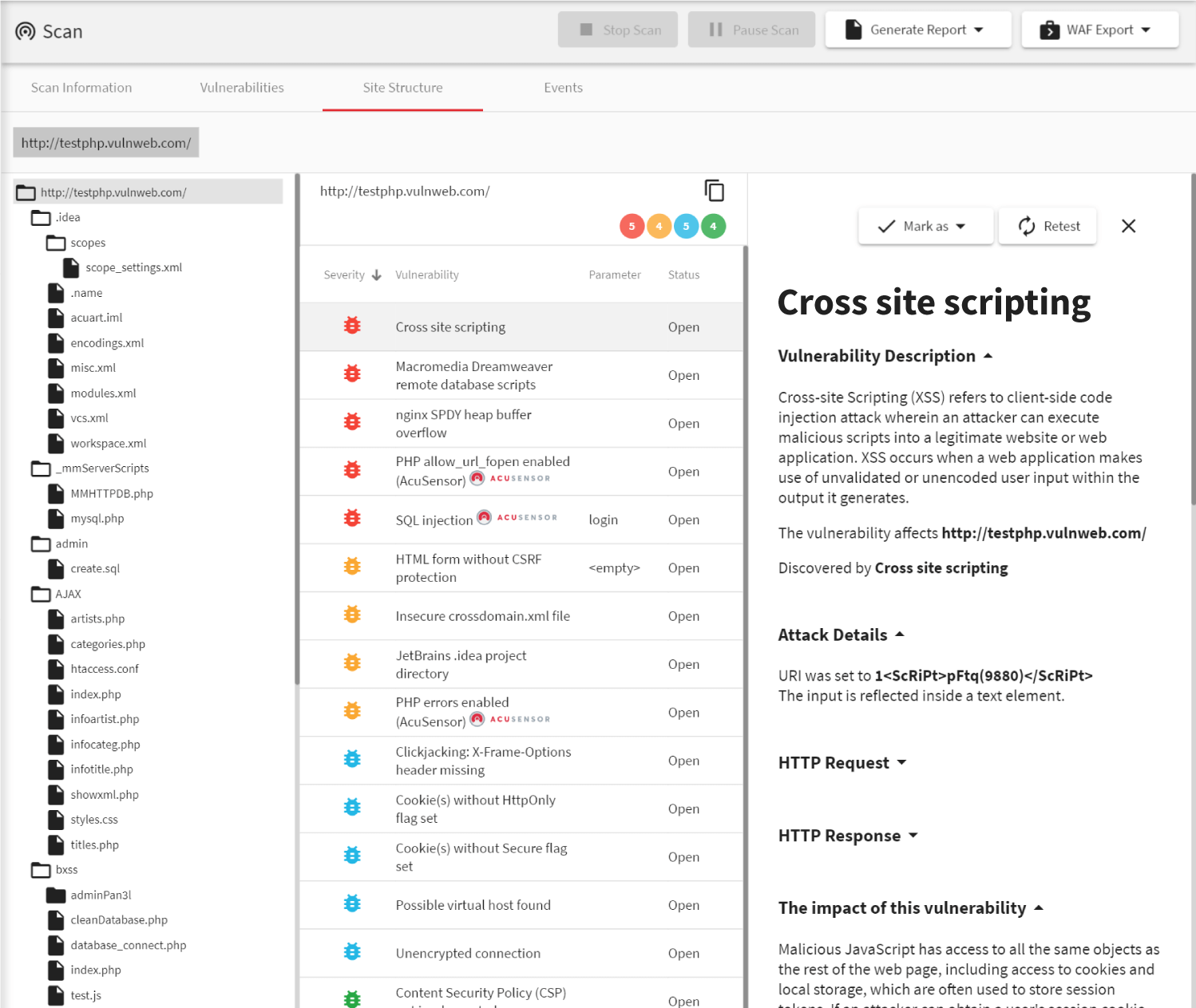
While many CSRF scanners can identify missing anti-CSRF tokens, Acunetix goes well beyond the basics by using highly-tuned heuristics to test for advanced variations of CSRF. Additionally, the Acunetix web application security scanner goes beyond CSRF tests and can look for even more serious vulnerabilities such as Cross-site Scripting and SQL Injection, too.
Thanks to its advanced crawler and JavaScript engine, DeepScan, Acunetix also has full support for modern single-page applications (SPAs) and can understand and fully test applications which rely on JavaScript frameworks like React, Angular, Ember, and Vue. This means Acunetix can understand an underpinning RESTful API when crawling a SPA. Since Acunetix can understand more than just JSON and XML, it can build a correct input scheme (an internal representation of the web application input), which it may then rigorously test for CSRF vulnerabilities.
Customizable Scop
When scanning large applications for CSRF vulnerabilities, it may be desirable to divide the scanning of the application up into smaller segments or scopes. A typical example of this would be when different development teams would be working on different parts of a large web application with different release cycles, and therefore, different scanning schedule requirements.
Acunetix makes customizing the scope of a vulnerability scan easy and painless. There are several ways to restrict the scope of a scan – you may choose to exclude pages you don’t want to scan manually or for more advanced users, Acunetix also supports excluding pages based on regular expressions.
Frequently asked questions
In a CSRF attack, the attacker first tricks the victim into clicking a link. The link causes the victim’s browser to send a command to a web application. The web application thinks that the command comes from the victim and executes it.
CSRF attacks may have serious consequences for the victim. For example, if there is a CSRF vulnerability in an online bank web application, the attacker may send a command that causes a money transfer from the victim’s bank account to the attacker’s bank account.
Read about a CSRF vulnerability that existed on Facebook and its potential consequences.
The only way to detect CSRF vulnerability is via manual penetration testing or automatic vulnerability scanning. We recommend that you use a vulnerability scanner because it’s much more efficient. Acunetix will find all potential web vulnerabilities, not just CSRF.
The best way to protect against CSRF is by using an anti-CSRF token. This is a special programming technique where the server generates a random value, stores it in a hidden field, and then verifies if the request sends this value, too. SameSite cookies may also help you prevent CSRF but this depends on the browser.
Recommended Reading
Learn more about prominent vulnerabilities, keep up with recent product updates, and catch the latest news from Acunetix.

“We use Acunetix as part of our Security in the SDLC and to test code in DEV and SIT before being promoted to Production.”
Kurt Zanzi, Xerox CA-MMIS Information Securtiy Office, Xerox