If anyone thought that big bugs would end with (a disastrous) 2014, 2015 looks as though it will also cause network admins to fret. The first in the series of BIG bugs for 2015 has just been uncovered. Nicknamed FREAK, this vulnerability breaks SSL, allowing man in the middle attacks, drastically reducing the use of SSL.
The attack is possible since millions of sites still allow “export-grade” cipher suites. These ciphers had been designed to be weak under pressure of US Government agencies who wanted to control the ciphers used in export products to be able to decrypt communication as needed. These export grade ciphers only made use of 512 bits.
Although the use of the weaker ciphers has been deprecated, since restrictions were lifted in the late 1990s, most web sites still allow them in order to support older systems. However most browsers and client software do not make use of the weak ciphers, so you might be thinking that we are all safe.
That is far from true, since researchers have identified a bug in OpenSSL which allows a man in the middle to intercept the SSL connection using a secure cipher, and replay the connection request using the weaker cipher to the server. The response from the server using the weaker encryption is forwarded to the vulnerable client and accepted due to the bug in OpenSSL.
The result is that the SSL connection is downgraded to a state that allows the attacker to crack it in just a few hours. This is reminiscent of the POODLE vulnerability, which also allowed the attacker to downgrade the TLS connection to make use of old encryption algorithms.
The solution involves patching all the client software that makes use of an unpatched version of OpenSSL. Users will have to wait for software vendors who use OpenSSL in their products to release updates with patched versions of OpenSSL.
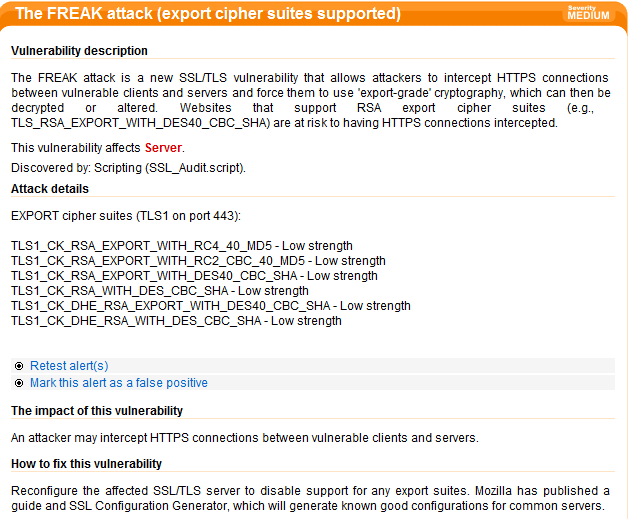
Servers should also restrict the use of older versions of SSL and deprecated encryption algorithms. Acunetix WVS has released an update which allows Web administrators and pen testers to detect if their website is vulnerable to FREAK.
At the time of writing, 12.2% of Alexa’s top 1 million domains are affected. Make sure that your website is not part of this FREAK statistic.
Get the latest content on web security
in your inbox each week.