Prevent Directory Listing
Directory Listing occurs when the web server does not find an index file (i.e. an index.php or index.html). If directory listing is turned on, the server will display an HTML page listing the contents of the directory.
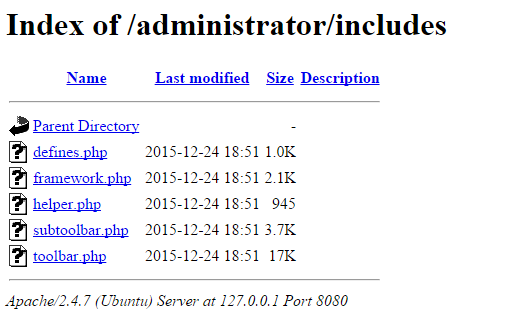
Disclosure of this information could make a site vulnerable to attacks by revealing information that can be used by an attacker seeking to exploit a vulnerability in a Joomla! plugin, theme, or even the web server itself.
While it is not a Joomla!-specific security measure to disable directory listing, several Joomla! sites running on default installations of Apache HTTP Server have directory listing enabled.
In order to disable directory listing in Apache HTTP Server, you will need to add the following configuration in your Joomla! site’s .htaccess file (this is usually located in your website’s root directory).
Options -IndexesProtect directories and files
It’s important to protect sensitive directories and files that can be used to write or upload files. Two such special directories in Joomla! are the logs and tmp directories.
Some extensions may use the logs directory to write logs that could contain sensitive information. By default Joomla! logs are not visible by public users, however, it’s advisable to restrict access to the logs directory, either by moving it out of the server’s web root, or by protecting the directory using your your Joomla! site’s .htaccess file (this is usually located in your website’s root directory).
The tmp directory is equally sensitive as it is used by Joomla! as a temporary directory for uploading extensions before installing them.
In order to disable access to these directories in Apache HTTP Server, you will need to create a new .htaccess file in both log and tmp directories with the following configuration line.
Deny from allRestrict access to the administrator Directory
Password protecting your Joomla! administration area through a layer of HTTP authentication is an effective measure to thwart attackers attempting to guess users’ passwords. Additionally, if attackers manage to steal a user’s password, they will need to get past HTTP authentication in order to gain access to Joomla! login form.
In Apache HTTP Server, you can achieve this by creating a .htpasswd file and adding a few configuration directives described below.
The .htpasswd file stores combinations of usernames and password hashes which the web server will use to authenticate users. You can create a .htpasswd file using the htpasswd command line or using an online password file generator.
Several Linux distributions install the htpasswd utility together with Apache itself, however, most Debian and Ubuntu users will need to install the apache2-utils package as follows.
sudo apt-get update sudo apt-get upgrade sudo apt-get install apache2-utils
Once htpasswd is installed, run the following command to create a new .htpasswd file with a single user. The following command will create a new .htpasswd file located at /srv/auth/.htpasswd with a username of myuser. htpasswd will then prompt you to enter and then confirm the password of your choice.
htpasswd -c /srv/auth/.htpasswd myuser.ht prefix are not served by Apache, however this should not be assumed.To enable basic HTTP authentication on the Joomla! administration area, you need to activate the directive described below on the administrator directory and reference the .htpasswd file created earlier. Insert the following lines into the appropriate <Directory> section of your server’s Apache configuration file or in an .htaccess file within the wp-admin directory.
AuthType Basic
AuthUserFile /srv/auth/.htpasswd
AuthName "Joomla! Authenticated area."
Require valid-userThe AuthType directive is specifying that the authentication type, in this case, Basic authentication is being configured.
The AuthUserFile specifies the full path to the .htpasswd file. This file is the file that shall be used to store password hashes which the server shall later use to authenticate users with.
The AuthName directive contains an arbitrary message which the browser will present to the user upon authentication. The Require valid-user setting simply instructs Apache to allow any valid user to authenticate.
While this file can be located anywhere on the filesystem, we strongly recommend that you do not place them in a web accessible directory. By default, all files beginning with .ht are not web-accessible in most default configurations of Apache, but this should not be assumed.
Enable HTTPS
Strictly speaking, HTTPS is not a protocol in and of itself, but it is rather HTTP encapsulated in TLS/SSL. TLS, or SSL, as it is commonly referred to, provides websites and web applications with encryption of data being transmitted and authentication to verify the identity of a host.
HTTPS is usually synonymous with shopping carts and Internet banking, but in reality, it should be used whenever a user is passing sensitive information to the web server and vice-versa.
Most sites do not necessarily need to serve their entire site over TLS, however, Joomla!’s login form and administration area, on the other hand, are the most sensitive areas of a Joomla! site. It is therefore strongly advised that TLS/SSL is not only implemented, but enforced in such areas.
Joomla! provides an easy way to enforce TLS/SSL on both the login and administration pages, as well as the option to enable TLS site-wide.
This is achieved by navigating to System > Global Configuration in the main administrative panel. Within the Server tab, in the Server Settings section, there are 3 options you can choose from.
- None (Not Recommended) — TLS will not be enabled at all on your Joomla! site
- Administrator Only (Recommended) — TLS will only be enabled for the administration panel on your Joomla! site
- Entire Site (Highly Recommended) — TLS will be enabled throughout your Joomla! site

Part 2
Configuration tips to secure your Joomla! installation
Get the latest content on web security
in your inbox each week.



