Easily two-thirds of the value of any given web vulnerabilities assessment comes from the use of automated web vulnerability scanners. At least that’s been my experience. I certainly don’t have the knowledge – or the time – to manually track down every single flaw on every single page of all the applications I test!
Like a carpenter, auto mechanic, or doctor, if we’re going to do a good job and obtain reliable results, we have to have good tools that automate the process wherever possible. Web vulnerability scanners are a core element of this approach.
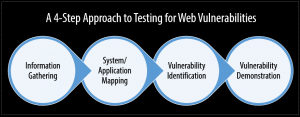
Following the ethical hacking methodology, there are four main steps involved when testing for web vulnerabilities:
- Information Gathering
- System/Application Mapping
- Vulnerability Identification
- Penetration (or, to minimize alarm, what I like to refer to as vulnerability demonstration)
A web vulnerability scanner comes into play in every step along the way. Other areas that scanners also add value are reporting and vulnerability remediation (going back and performing quick checks to ensure a flaw has been fixed).
Something we’ve all experienced is the universal law that says you cannot change facts but you can change problems. Applying this to web security, we cannot change things such as the threats we face and the complexity of any given web application’s codebase. But we can change the problems we have such as the lack of visibility and control of our web environments and, most importantly, the lack of time – the scarcest resource of all. These problems can be solved, in part, by using a web vulnerability scanner that automates the process.
We can’t live without automated web vulnerability scanners, but we also need to make sure we balance our testing with additional analysis in areas that need it. This may include web forms and login mechanisms. Even certain findings such as SQL injection or weak passwords may need further manual validation or exploitation. It’s all a balancing act. The wise web security professional will not only trust but verify but use automation to his advantage.
Those who believe they can tackle all web security vulnerabilities with mere brawn and brainpower are delusional. Given the overall complexity of any given environment combined with the number of people who need to know, right now, where things stand, you have to automate your web vulnerability testing. Otherwise you’ll fall behind the criminal hackers and not have a true sense of your overall information risks.
Step back and look at the big picture. Get out of the techie rut that’s so easy to fall in to. Time is of the essence – business has to get done. Smart automation is the only way to keep up.
Get the latest content on web security
in your inbox each week.