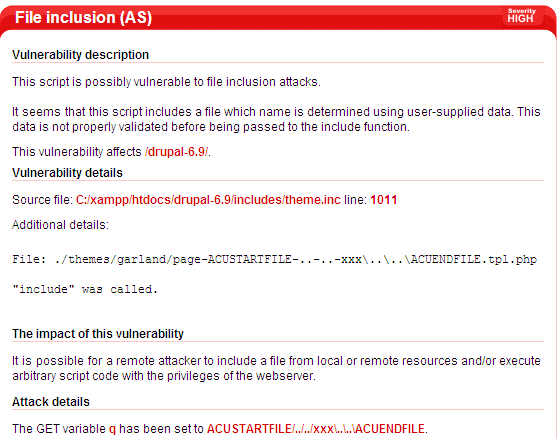
I was testing our scanner (with AcuSensor enabled) on Drupal (http://www.drupal.org) and the scanner found a possible File Inclusion vulnerability.
As you can see from the screenshot above, the GET variable q was set to start/../../xxx….end and it got partially sanitized. It reached the include function as /themes/garland/page-start-..-..-xxx….end.tpl.php. All the slashes were replaced with “-“.
Even more, we cannot fully control the include path, the user input is automatically prefixed with ./themes/garland/page-. So, this vulnerability doesn’t look exploitable, right? Actually this is exploitable on Microsoft Windows systems.
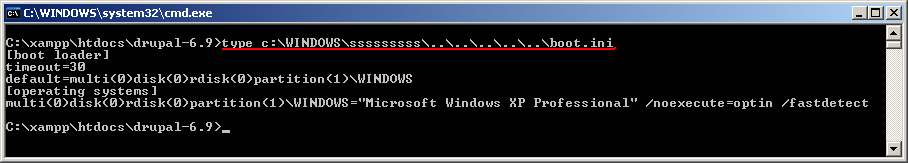
On Unix systems, something like “cat /var/www/some_invalid_filename/../../../../../etc/passwd” doesn’t work because some_invalid_filename is not a directory and give the error that some_invalid_filename doesn’t exist. It will not work even if you have a valid file name.That’s the expected behavior in my opinion, however, in Microsoft Windows things are different.
Executing the command “type c:windowssssssssssssss……….boot.ini” will return the contents of c:boot.ini even if sssssssssssss is not a directory and it doesn’t even exists as a file name. Check the screenshot below.
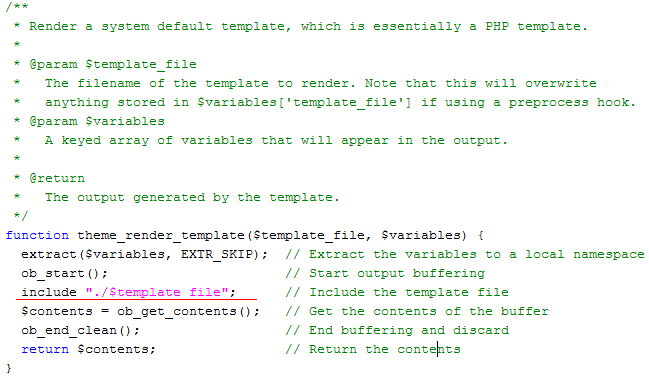
The vulnerability is located in the file “includestheme.inc” on line 1011. Vulnerable code:
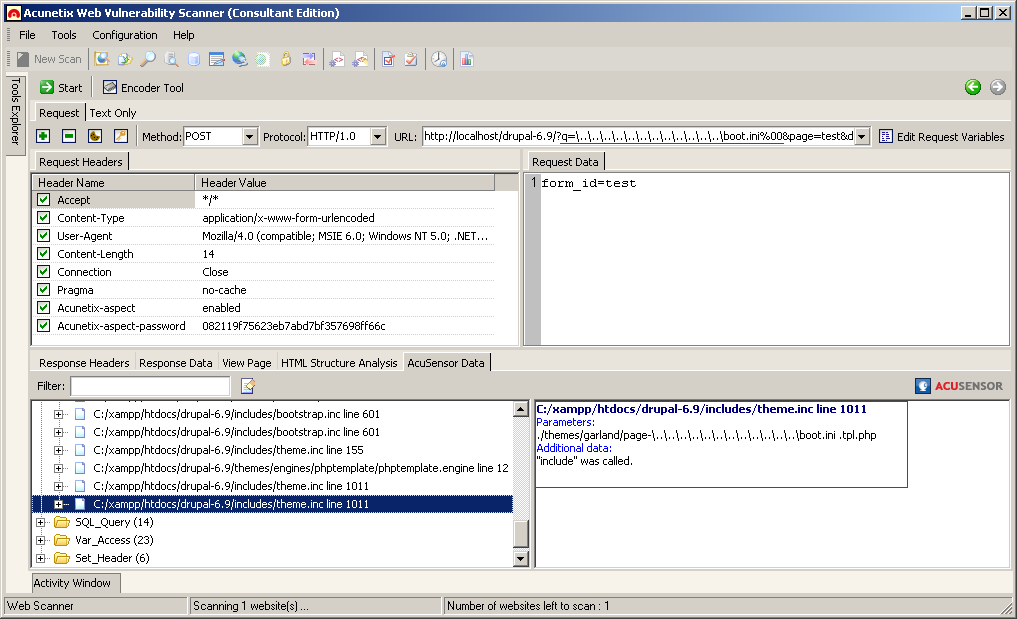
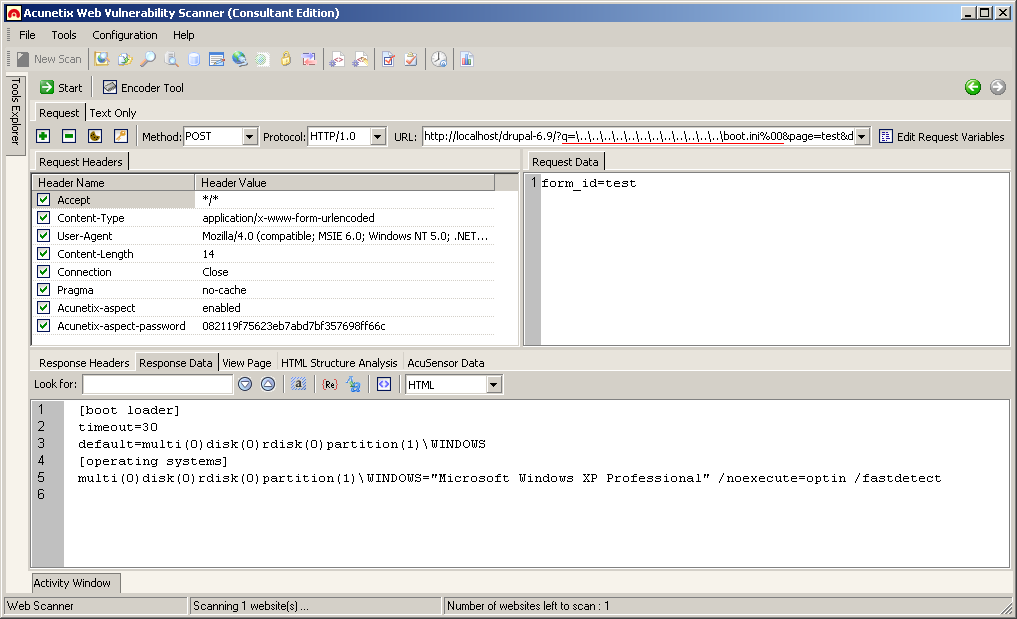
PHP option magic_quotes_gpc is turned OFF in Drupal, so it’s possible to use %00 to terminate the string. Therefore, if you set q to something like q=……………………boot.ini%00 it is possible to include the contents of boot.ini on Windows systems, if the web server is installed on the C: partition. Below are two more screenshots about the exploit.
Drupal versions 5.x and 6.x are vulnerable to this problem.
Drupal security team was notified about this vulnerability on 29 January 2009 and they’ve released a fix on 25 February 2009. The fix for Drupal version 5.x is available here. And for Drupal version 6.x can be found here.
Get the latest content on web security
in your inbox each week.