Yesterday, an update was released for Acunetix Vulnerability Scanner which includes a test for a critical OpenSSL vulnerability named The Heartbleed Bug (CVE-2014-0160).
Quote from the report:
The Heartbleed Bug is a serious vulnerability in the popular OpenSSL cryptographic software library. This weakness allows stealing the information protected, under normal conditions, by the SSL/TLS encryption used to secure the Internet.
A few notes about the Heartbleed Bug vulnerability:
- It affects many products that are using OpenSSL, the most notable being the two most widely used open source web servers – Apache and nginx.
- Using this bug an attacker can read up to 64k bytes from the application memory.
- OpenSSL versions 1.0.1 through 1.0.1f (inclusive) are vulnerable.
- It doesn’t affect the IIS web servers, so ASP.NET based web applications are safe.
- It affects products where the heartbeat extension (RFC6520) is enabled (and it often is).
- The bug was introduced with OpenSSL release 1.0.1 on 14th of March 2012.
- A large number of top sites were affected by this bug Heartbleed Alexa top 10000 including Yahoo, Flickr and Tumblr.
- The fix includes upgrading to the latest version of OpenSSL to close the information leakages. It may take some time for all the vendors implementing SSL using vulnerable OpenSSL implementaitons to upgrade.
- Exploiting this vulnerability doesn’t leave any traces in the logs and therefore it’s not possible to know if your site was targeted or not. If somebody already used this vulnerability to leak sensitive data, there is no way to know about this.
In our internal testing, I’ve learned that session cookies are very often leaked when exploiting this vulnerability.
Using session cookies, an attacker can hijack a valid session and gain access to the application without the need to provide any credentials. The server leaks what resides in the application memory at the time when the vulnerability is being exploited.
So, if somebody visits a WordPress Dashboard page it’s very probable that it would leak the WordPress session cookies. I’ve also seen leakage of nginx configuration files, username and passwords, private messages, HTML response data and other sensitive data.
An attacker can continuously connect and exploit this vulnerability again and again, each time leaking more and more information from the server memory.
Various data that was leaked during our internal test:
To conclude, this vulnerability is very, very dangerous. Remember that you have no way of knowing whether this vulnerability has already been exploited since it leaves no traces in the logs. It’s not possible to go back and find out whether someone used this vulnerability to leak sensitive data from your web application.
I highly recommend to scan your website using the latest version of Acunetix Vulnerability Scanner to check if your website is vulnerable. Both the on-premises (software download) Web Vulnerability Scanner and Online Vulnerability Scanner can scan for and detect this vulnerability.
Step-by-step guide to updating your version of Acunetix WVS (on-premises version)
Note: Follow these steps for the on-premises version only – the online version is updated automatically.
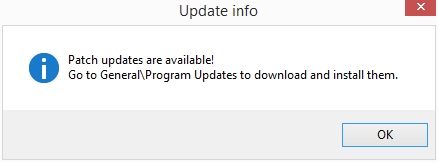
Step 1
When opening Acunetix WVS, a check for new Patch Updates is made – Acuentix WVS will notify you that Patch Updates are available.
Step 2
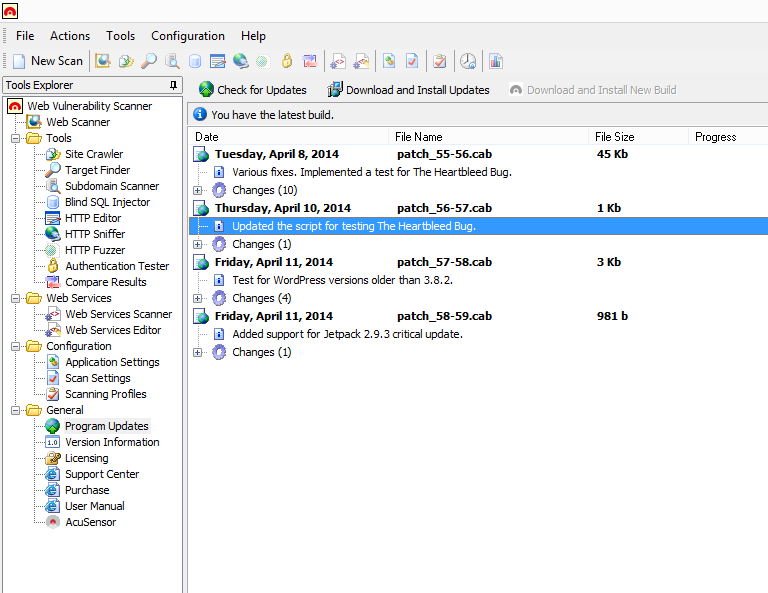
Navigate to Help > Check for Updates, or alternatively, Tools Explorer > General > Program Updates.
The available Patch Updates will be listed.
Step 3
Click the ‘Download and Install Updates’ button to install all the available Patch Updates.
Acunetix WVS will notify you that the installation of Patch Updates has been successful.
Get the latest content on web security
in your inbox each week.