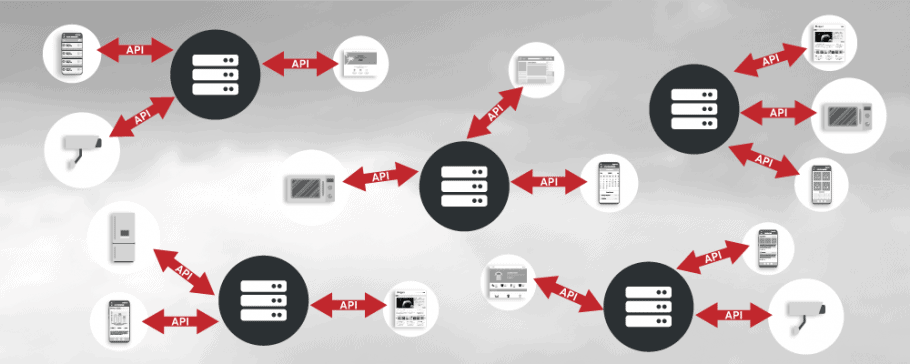
It’s no secret – application programming interfaces are everywhere. Many complex web applications are based on microservices, which use APIs to work with one another. Mobile apps and IoT devices also use APIs to communicate with their back-ends. Not to mention that almost every online tool nowadays makes its functionality available via an API.
Web API Security – Important but Not Easy
Securing APIs is even more important than securing your endpoint computers and your networks. In the past, most businesses relied on applications installed on personal computers and sensitive data stored on local servers, connected using complex internal networks. Now, most businesses, from startups all the way to enterprises, rely on the cloud and web services. Personal computers with browsers are just thin clients for web applications and APIs. Internal networks are just there to connect to the Internet. This means that to prevent data breaches, you must focus on security issues related to your web resources.
However, attaining web API security is not an easy task because, just like web applications, APIs are usually custom-built. It’s not as simple as turning on SSL/TLS to encrypt communications, finding a virus using its signature, or discovering that your Windows needs an upgrade. To check an API for vulnerabilities, the tool must analyze the runtime application by sending HTTP requests that contain custom HTTP headers and payloads that imitate the actions of end-users.
APIs use the same languages and technologies as web applications. They are also prone to the same types of security risks and attacks, for example, SQL injection attacks. However, APIs are just discrete endpoints. If the security scanner doesn’t know where to find them and how to access them, it can’t verify their security.
Luckily, APIs are mostly built following common API management and design standards. They have definition files in descriptive languages, which specify exactly where to find each endpoint, how it works, and how to communicate with it. Such information is enough for a web vulnerability scanner to be able to check web API security.
How to Secure APIs with Acunetix
Acunetix is your number one choice for securing your web APIs. It is not only one of the best web vulnerability scanners on the market but it also supports all the traditional and modern API technologies.
With Acunetix, you can scan the following types of APIs:
- SOAP APIs (web services) – while SOAP popularity is on the decline, a lot of applications are still based on SOAP web services. Acunetix can easily scan such services, for example, using a WSDL file.
Read a tutorial that shows how to scan a SOAP web service using Acunetix. - REST APIs – JSON-driven representational state transfer APIs remain the most popular API technology and, of course, Acunetix can fully scan RESTful APIs for vulnerabilities, for example, using an OpenAPI specification, a Swagger specification, or a WADL file.
Read a tutorial that shows how to scan a REST API using Acunetix. - GraphQL APIs – Acunetix is a leading-edge tool and supports modern, emerging technologies, for example, GraphQL. GraphQL has been recently gaining more and more attention and popularity and Acunetix is one of the very few tools that can verify the security of GraphQL APIs.
Read a tutorial that shows how to scan a GraphQL API using Acunetix.
However, as long as your API uses web technologies and as long as you provide a list of endpoints, you can use Acunetix to scan other types of APIs, too. You can even import your endpoints from a simple text file with a list of URLs.
That’s not all. Even if you don’t have the list of endpoints, all you need for Acunetix to work is to be able to install a tool such as Fiddler or Paros as a proxy to intercept API requests to your website API or API gateway in order to collect endpoint locations and the API call syntax. You can then export the list of endpoints to be used by Acunetix.
Advantages of Using Acunetix for Web API Security
Here are some more reasons why Acunetix is your best choice for discovering and eliminating API vulnerabilities.
- Acunetix supports all vulnerabilities defined by OWASP (Open Web Application Security Project) in the OWASP Top 10 list and much more. Unlike most vulnerability scanners, Acunetix can actually perform validation and provide evidence that the vulnerabilities are real.
- Your security teams don’t have to worry about API access control. Acunetix supports many common standards used to authenticate, for example, basic authentication and OAuth 2.0. If your API is accessed via a web interface, you can additionally use the Login Sequence Recorder to handle non-standard auth mechanisms.
- Acunetix supports a lot of integrations out of the box. For example, you can export the API vulnerabilities that you find and import them directly into web application firewalls so that you have temporary real-time protection until your developers resolve the security issues.
Of course, Acunetix is the starting point for your API security and cannot be considered the only tool needed for the job. Just like in the case of web applications, to attain more security you can employ additional tools, for example, source code analyzers, as well as security mechanisms, for example, distributed denial-of-service (DDoS) protection. However, web vulnerability scanning is the technology that brings you the most benefits from the start.
Get the latest content on web security
in your inbox each week.





