Recently there were a lot of news reports about an ongoing attack on sites using WordPress software. Attackers are using around 90,000 computers to try to brute force WordPress credentials. All these servers are trying common account names like admin, administrator, test, tom, jessica, … and common passwords like admin, 123456, password, … against a wide rage of WordPress installations. You can find the complete list of tested usernames and passwords on Brian Krebs’s website.
If you analyze this list of usernames/passwords, you will realize that it basically includes common passwords (like password), common keyboard combinations (like qwerty), common number combinations (like 1234567890) and a big list of English names/words/variants. I also found the word parola in the list of tested passwords. This is interesting because the word parola is a Romanian word equivalent for password. I did not find variants of the word password in other languages which leads me to believe that it’s probable the author(s) of this attack are from Romania. This is somewhat expected considering that Romanians are responsible for a large number of brute force attacks against SSH.
The latest build of Acunetix WVS includes new scripts that will test for various WordPress security issues. The rest of the article describes these new checks, as well as another check for open Amazon S3 buckets.
One of these scripts uses various techniques to enumerate usernames for WordPress users. When the script manages to identify valid usernames, it will list them in a Knowledge Base article similar to the one shown below.
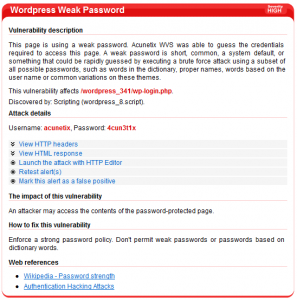
The same script will then proceed to try and guess the passwords for the list of users harvested from WordPress. It will initially use a list of common passwords. In addition, the script tries to derive passwords from various sources such as the username, the hostname, the name of the site, and from words which are repeated on the main WordPress page. If one of the passwords match, an alert similar to the following will be shown:
In this case, the scan discovered the username ‘acunetix’ and found that its password is the username written in leetspeak (acunetix => 4cun3t1x). A lot of people are using leetspeak when choosing passwords.
Another script tries to determine what WordPress plugins are installed. It is using a constantly updated list of the most popular WordPress plugins. The script will also try to identify plugins using links that include plugins’ name (such as /wp-content/plugins/wp-syntaxhighlighter/). The script will then try to determine the version of each plugin identified. The script generates a list of plugins identified, showing the version installed, and the latest version for the same plugin, allowing you to easily determine which ones need to be updated.
In our example installation, the WordPress plugin wordpress-seo is installed with version 1.4.6 but the latest available version is 1.4.7.
And finally, unrelated to the WordPress brute force attacks, another script included in the latest build will test for open Amazon S3 buckets. Metasploit guys published a very interesting article about websites using open Amazon S3 buckets. An open Amazon S3 bucket is a bucket where anybody can list the contents of this bucket. This is usually a security risk because the bucket can contain files that are not intended for public, such as source code or backup files. The latest Acunetix WVS build checks if a website is using Amazon S3 buckets and verifies that the contents of the bucket cannot be listed.
Get the latest content on web security
in your inbox each week.