MANAGE YOUR WEB SECURITY WITH
Acunetix vulnerability scanner for web applications and APIs
Improve your application security with the Acunetix vulnerability scanner
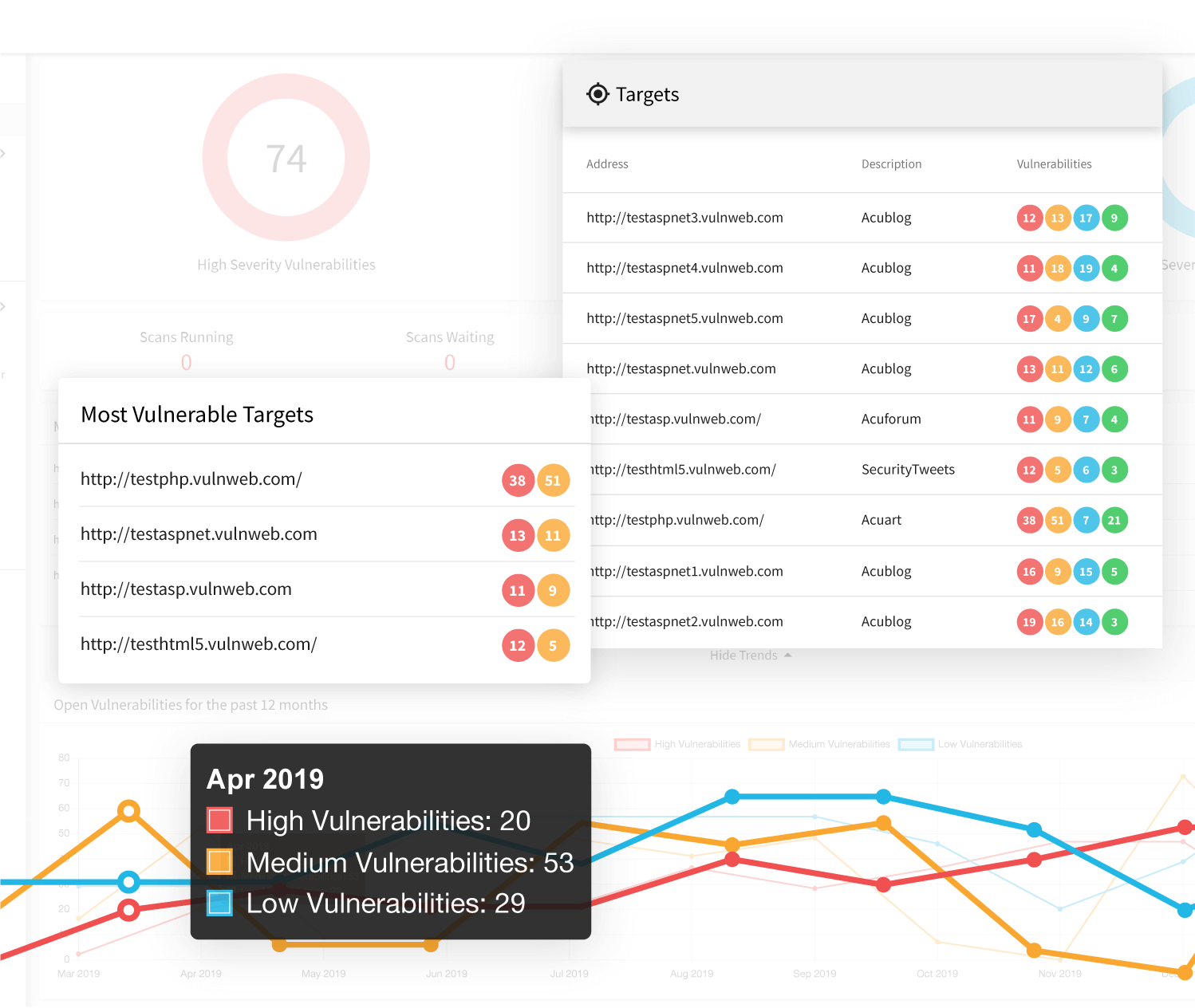
Acunetix is a vulnerability scanner designed to help organizations identify, validate, and fix security vulnerabilities in their web applications and APIs. By combining automated scanning with built-in validation, it enables security teams to focus on real, exploitable risks rather than chasing false positives.
Modern vulnerability scanning tools cover a wide range of systems, from operating systems and open ports to cloud infrastructure and applications. Acunetix is purpose-built for the web layer – testing running applications and APIs from the outside in, as hackers would during a cyberattack.
With support for thousands of known vulnerabilities and CVEs, automated proof of exploit for many findings, and integrations across development workflows, Acunetix strengthens your security posture and helps reduce the risk of a data breach.
What is a vulnerability scanner?
A vulnerability scanner is a cybersecurity tool that automatically tests systems for security gaps and known weaknesses. It sends crafted requests to a target system and analyzes responses to identify vulnerabilities that could be exploited by attackers.
There are several types of vulnerability scanners, including:
- Network vulnerability scanners that assess infrastructure, open ports, and firewall exposure
- Cloud and container scanners that evaluate modern environments
- Software composition analysis tools that identify vulnerable dependencies
- Web application and API scanners that test running applications for exploitable flaws
Acunetix focuses on web application and API vulnerability scanning using dynamic application security testing (DAST). This approach analyzes applications in their running state, helping with identifying vulnerabilities that are actually exposed and reachable by cyber threats.
What to look for in a web and API vulnerability scanner
Not all vulnerability scanning tools are equally effective for modern applications. When evaluating a solution, several capabilities make a measurable difference:
Accuracy and validation
Automated scanning often produces large volumes of results, many of which require manual verification. Look for tools that support reliable vulnerability detection and validation. Acunetix uses proof-based scanning to confirm many findings, reducing noise and supporting efficient vulnerability management.
Coverage of modern applications and APIs
Today’s applications rely heavily on JavaScript frameworks and APIs. A scanner must handle complex functionality, authentication flows, and API endpoints to provide meaningful attack surface coverage.
Depth of testing
Effective vulnerability assessment depends on reaching all relevant parts of an application, including authenticated areas and business logic. Without this depth, critical security vulnerabilities may remain hidden.
Automation and integration
To support DevSecOps workflows, scanning must integrate with CI/CD pipelines and issue tracking systems. Real-time or near real-time feedback helps teams respond quickly to emerging cyber threats.
Actionable remediation and prioritization
Security professionals need more than raw findings. Clear prioritization and remediation guidance help teams fix issues efficiently and close security gaps faster.
Why choose Acunetix for vulnerability scanning?
Acunetix is a DAST-first vulnerability scanner built to identify and validate security vulnerabilities in running web applications and APIs. It helps organizations reduce risk by focusing on vulnerabilities that can actually be exploited.
Focus on real, exploitable risk
By testing applications from the outside in, Acunetix identifies vulnerabilities that are visible within your attack surface. This perspective aligns with how hackers operate and supports better prioritization.
Built-in validation to reduce false positives
Acunetix uses proof-based scanning to automatically confirm many vulnerabilities. This improves vulnerability detection accuracy and reduces time spent verifying results.
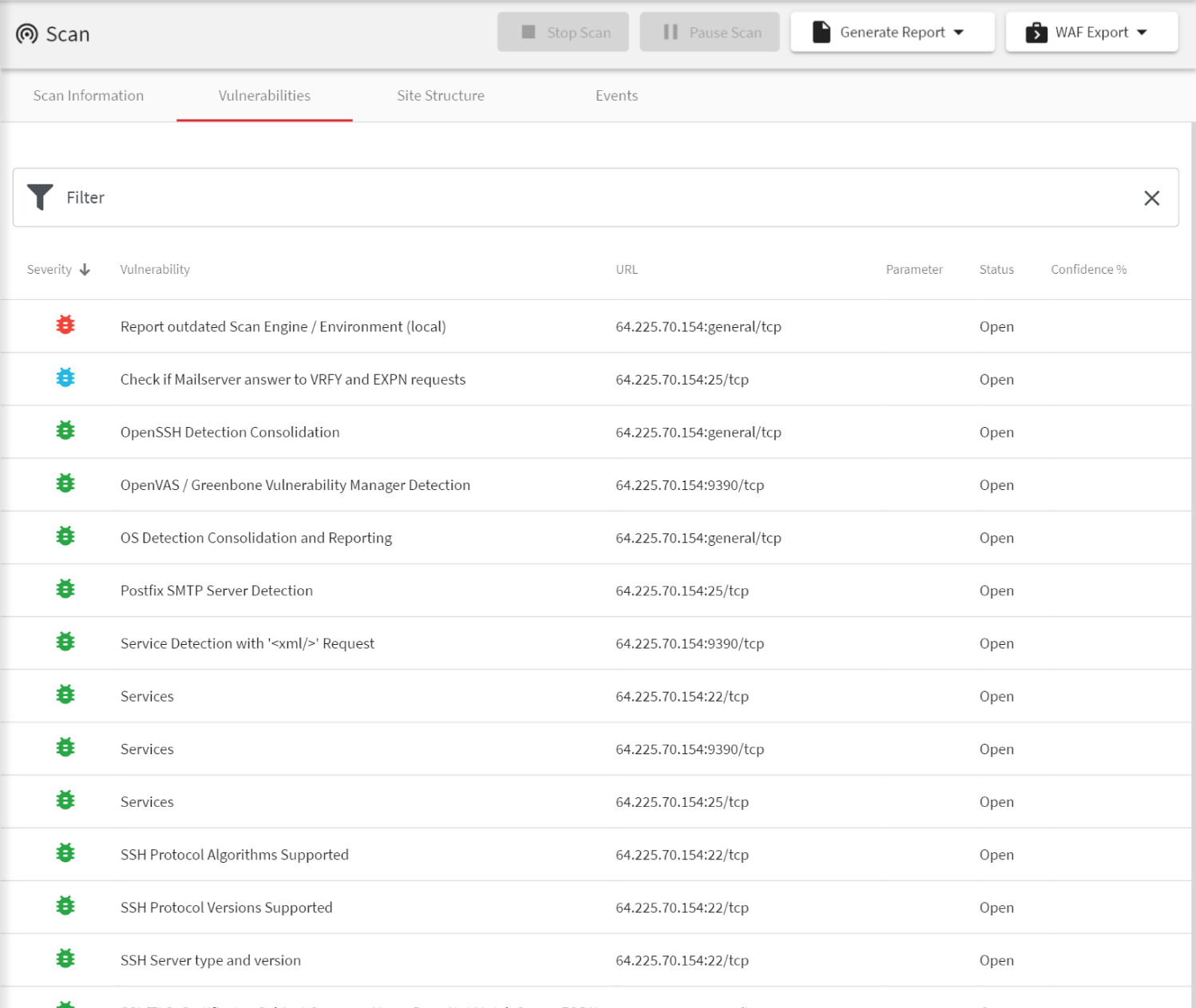
Broad vulnerability coverage
The scanner detects a wide range of issues, including injection flaws, cross-site scripting (XSS), authentication weaknesses, misconfigurations, and API vulnerabilities. It helps organizations address risks aligned with industry standards and common vulnerability databases.
Support for modern architectures
Acunetix is designed for modern SaaS and web environments, including dynamic applications and API-driven architectures. It can test complex functionality across distributed systems.
Scalable and flexible deployment
Organizations can deploy Acunetix on premises or as a SaaS solution and scale scanning capacity as needed. This flexibility supports both small teams and enterprise security programs.
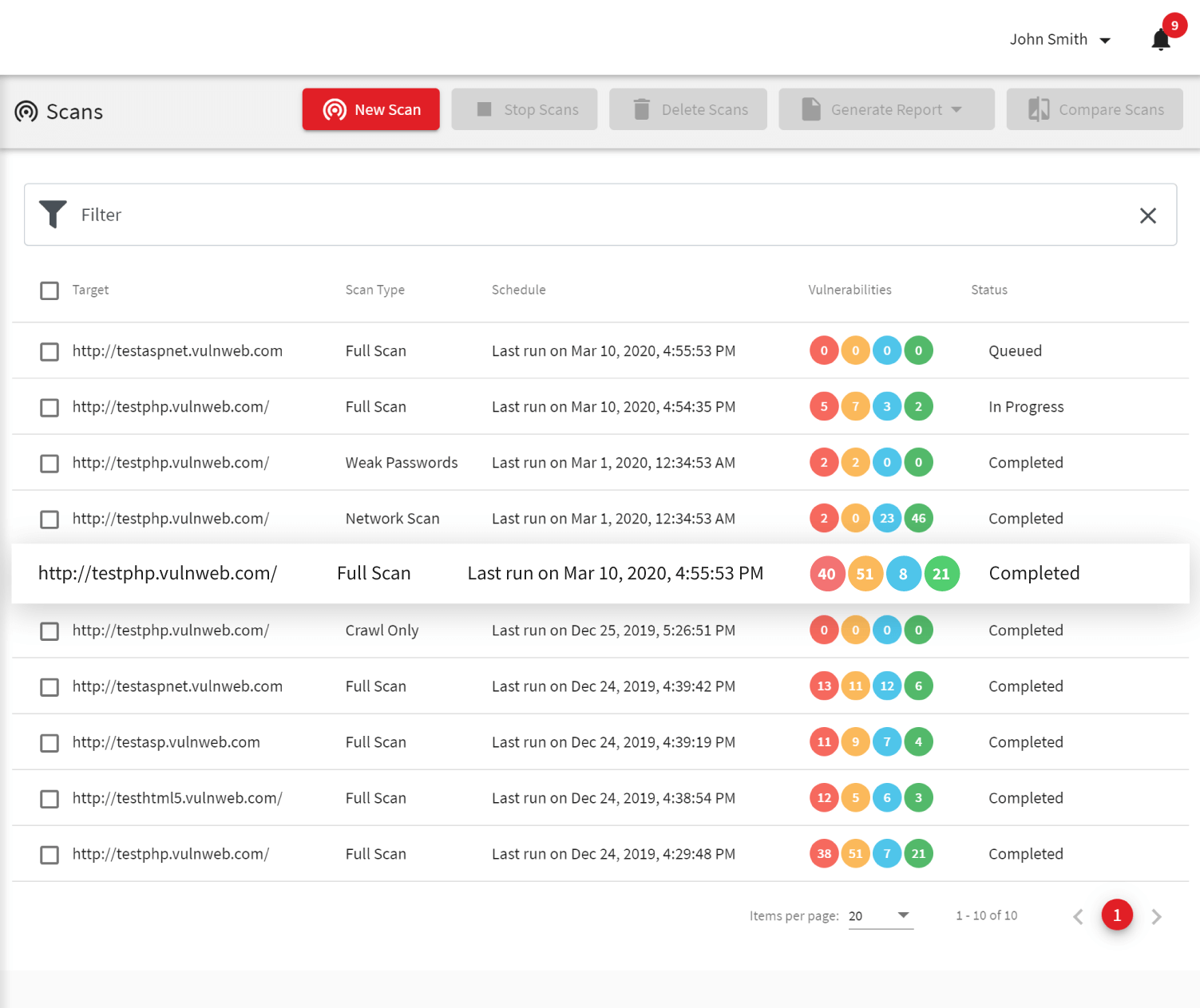
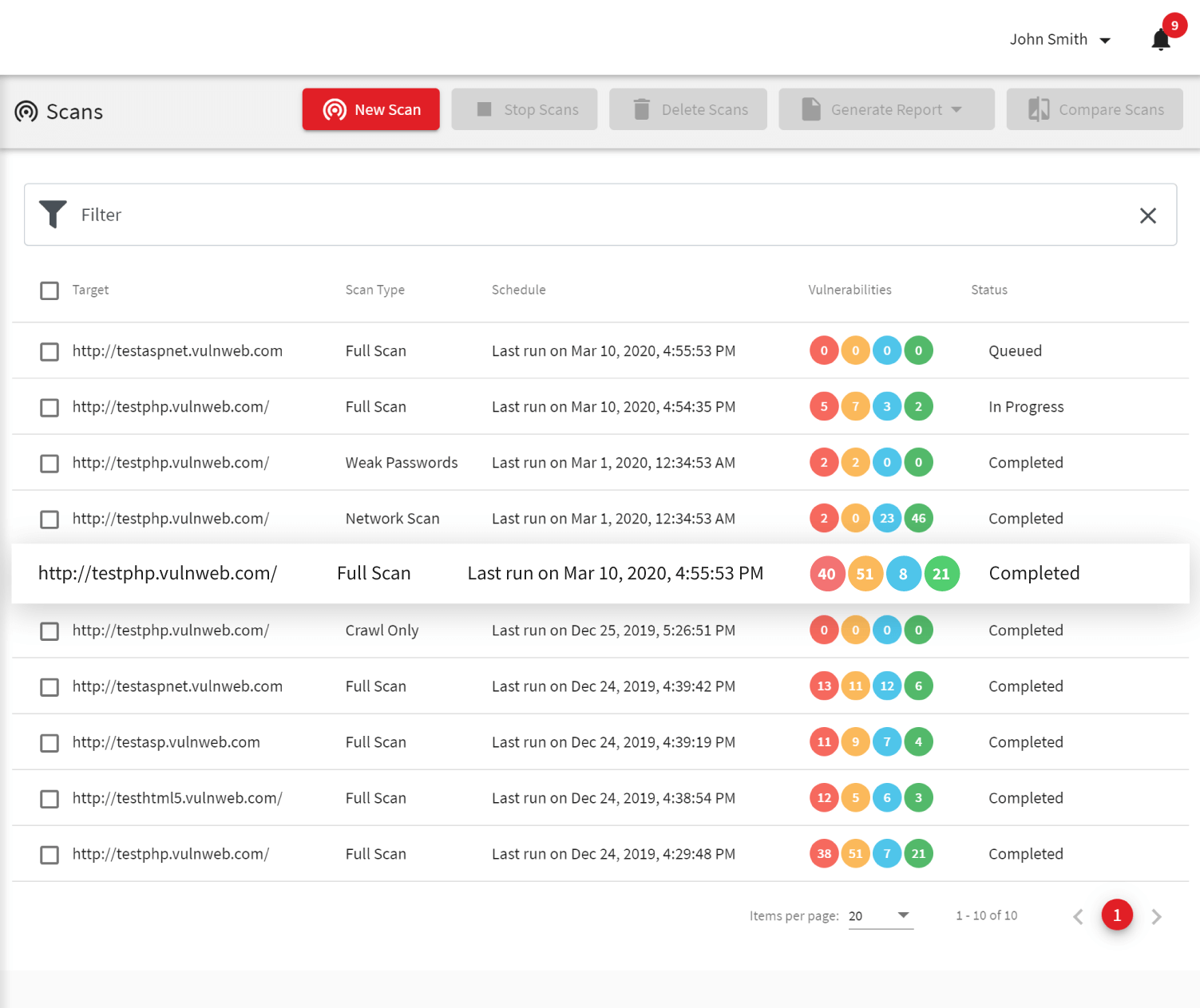
Automate vulnerability scanning across your SDLC
To keep up with modern development cycles, vulnerability scanning must be continuous and integrated into existing workflows.
Acunetix supports:
- Integration with CI/CD pipelines for automated scanning
- Connections to issue trackers such as Jira, GitHub, and GitLab for streamlined vulnerability management
- APIs for extending functionality and integrating with internal tools
- Distributed scanning to handle large and complex environments
By embedding vulnerability assessment into the software development lifecycle, security teams and developers can identify vulnerabilities earlier and reduce the likelihood of successful cyberattacks.
To see how Acunetix fits into your application security program, request a demo to explore its vulnerability scanning capabilities in a real-world environment.
Frequently asked questions
A vulnerability scanner is an automated cybersecurity tool that tests systems for known security vulnerabilities and misconfigurations. It helps organizations identify vulnerabilities that could lead to exploitation or data breaches.
A vulnerability scanner automates vulnerability detection across a broad attack surface, while penetration testers perform targeted, manual pentesting to simulate real-world attacks. Both are important for a complete security strategy.
An automated vulnerability scanner sends requests that mimic attacker behavior and analyzes responses to detect weaknesses. If a vulnerability is found, the tool reports it with details to support remediation and vulnerability management.
Acunetix detects a wide range of web application and API vulnerabilities, including SQL injection, cross-site scripting (XSS), authentication issues, misconfigurations, and other security vulnerabilities that could expose sensitive data.
Recommended Reading
Learn more about prominent vulnerabilities, keep up with recent product updates, and catch the latest news from Acunetix.

“We use Acunetix as part of our Security in the SDLC and to test code in DEV and SIT before being promoted to Production.”
Kurt Zanzi, Xerox CA-MMIS Information Securtiy Office, Xerox