Beyond Low-Hanging Fruit
The Acunetix RFI scanner tests for both local file inclusion (LFI) and remote file inclusion (RFI). While many file inclusion vulnerability scanners can find low-hanging file inclusion, Acunetix goes well beyond the basics thanks to its advanced crawler and JavaScript engine called DeepScan. Thanks to DeepScan, Acunetix also has full support for modern single page applications (SPAs) and can understand and fully test applications that rely on JavaScript frameworks.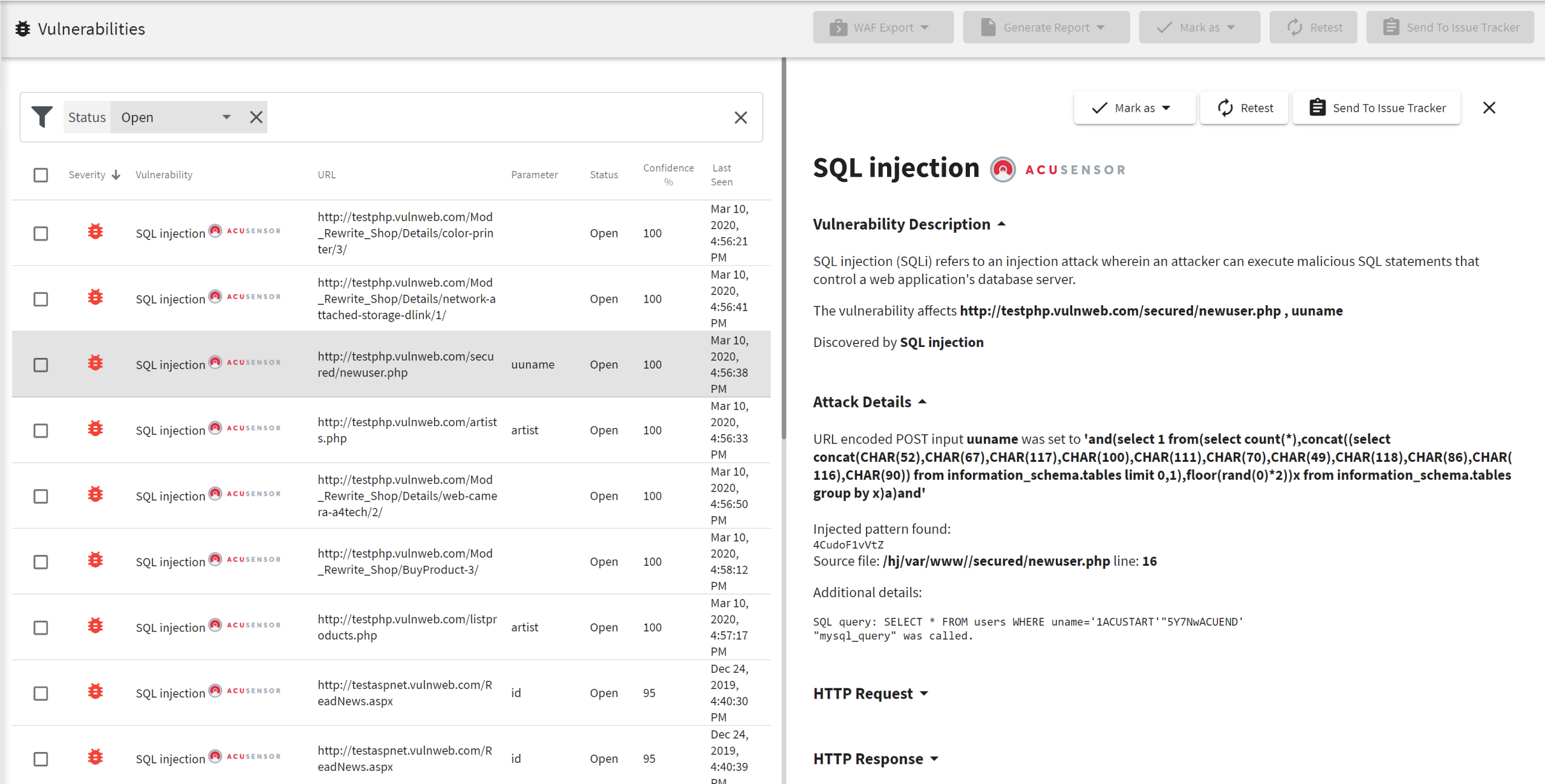
Runtime Source Code Analysis
In addition to being a fully automated black box scanner (no knowledge of back end code), Acunetix also provides AcuSensor as part of its standard offering. AcuSensor is a an optional sensor for Java, ASP.NET, and PHP applications that can easily be deployed on the application backend to analyse source code while it is in execution by the scanner, giving even more accurate results and even fewer false positives.Frequently asked questions
The best way to discover and then eliminate RFI vulnerabilities (remote file inclusion) is by using a vulnerability scanner. Web application firewalls (WAF) do not help you discover or prevent vulnerabilities, just make it difficult (but not impossible) for attackers to exploit them. With a vulnerability scanner, you can quickly identify and then eliminate all your vulnerabilities.
RFI vulnerabilities are very dangerous. If an attacker can include a remote file, they can potentially establish complete control over the web server. If the web server has other vulnerabilities, the attacker may propagate the attack to your other systems. RFI is also commonly used in conjunction with many other techniques, for example, phishing.
Read how attackers are using RFI in dangerous phishing campaigns.
Once you use Acunetix to detect an RFI vulnerability, you can eliminate it by modifying the application code so that you do not include any files based on user input. If this is not possible, you must maintain a whitelist of files that can be included.
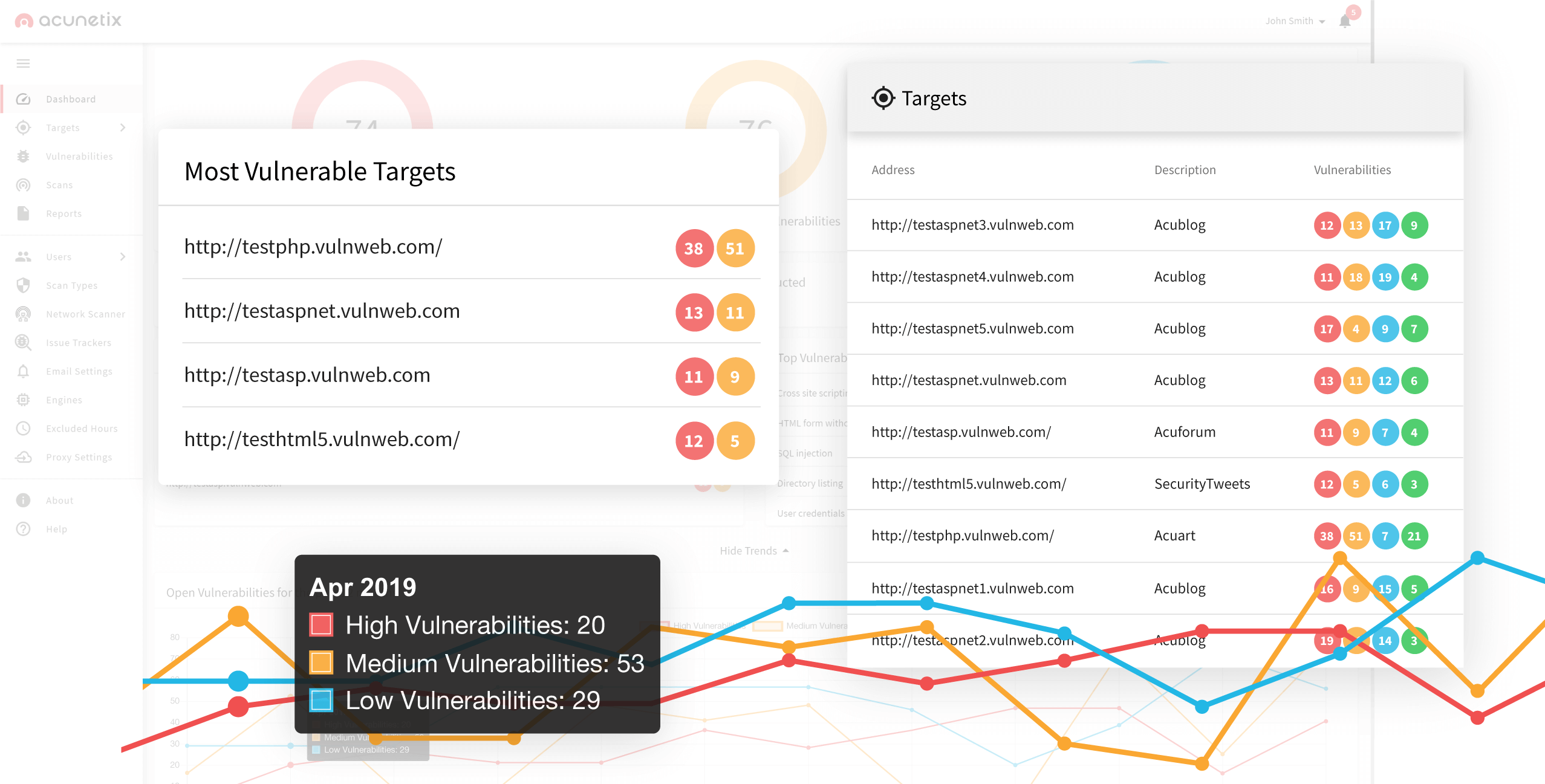
Acunetix can detect web vulnerabilities (for example, SQLi, XSS, CSRF, SSRF, LFI, RCE, and many more), but it is more than just a simple scanner. Acunetix also comes with a full set of vulnerability assessment and vulnerability management features, and it integrates with many issue tracking tools, CI/CD, and other software.
Recommended reading
Learn more about prominent vulnerabilities, keep up with recent product updates, and catch the latest news from Acunetix.

“We use Acunetix as part of our Security in the SDLC and to test code in DEV and SIT before being promoted to Production.”
Kurt Zanzi, Xerox CA-MMIS Information Securtiy Office, Xerox