SQL Injection Scanner: Enter Acunetix
SQL Injections have been the number one critical vulnerability on the OWASP Top 10 list since its first edition in 2010 and they are expected to hold that spot in the future. SQL Injection vulnerabilities can have very serious consequences for the business, such as sensitive information theft (for example, credit card numbers). In the worst cases, the attacker may be able to get full control of the web server. They are also commonplace and are relatively easy to exploit simply by using Google search to find suitable malicious code examples for SQL queries. That is why you need an SQL Injection scanner to protect your web applications against such security flaws. Acunetix is the most renowned web application security scanner and SQL Injection flaws have always been its very strong focus. The Acunetix web security solution is available on-premises for Windows, Linux, and macOS, as well as an online service.
Detecting All Types of SQL Injections
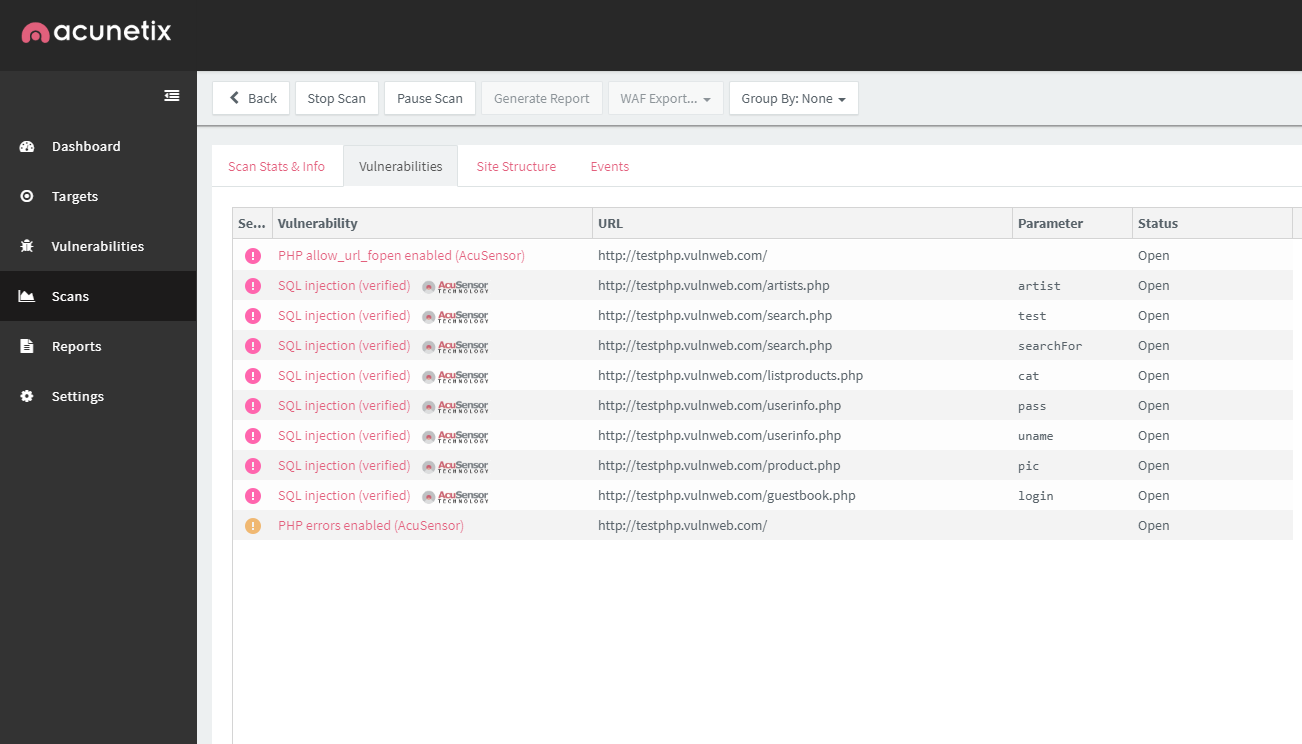
While simple SQL Injections are easy to detect and every open source and commercial web vulnerability scanner can handle them, some testing tools may be unable to detect the more advanced versions of SQL Injection attacks. Acunetix performs SQL Injection tests for all the following SQL Injection techniques.
- Classic SQL Injections are also called In-Band SQL Injections. They are the easiest to find and exploit. In such cases, the intruder launches the attack on the database server using malicious SQL statements delivered via user input and receives results using the same channel.
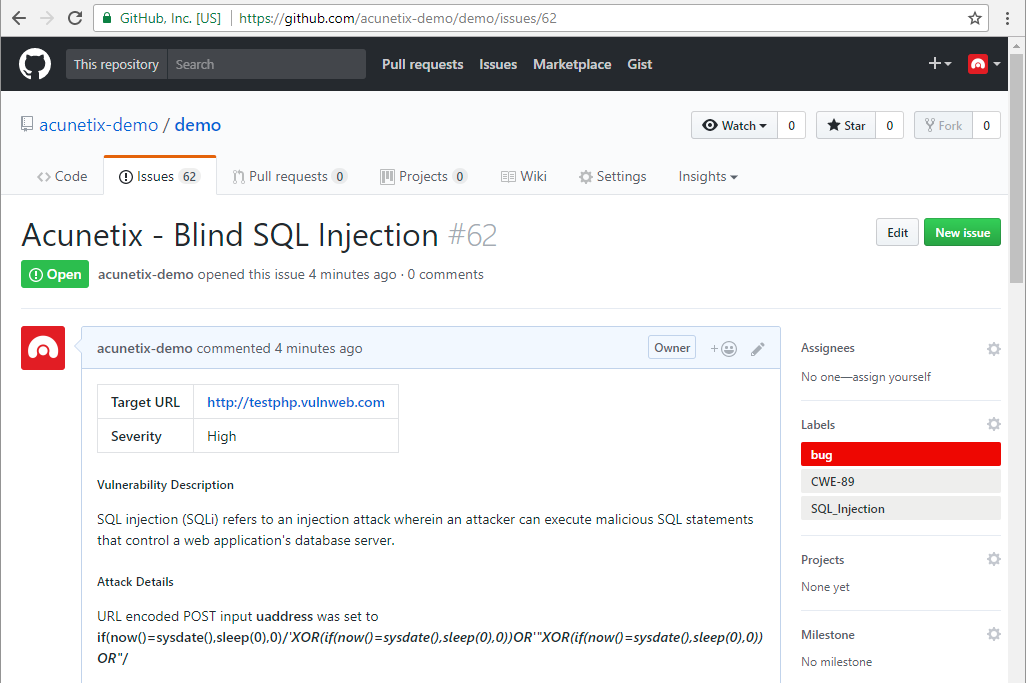
- Blind SQL Injections, also called Inferential SQL Injections, are much more difficult to detect and exploit because the attacker is unable to directly see the results of the SQL commands. Acunetix is a blind SQL Injection scanner thanks to its unique AcuMonitor technology.
- Out-of-Band SQL Injections are the most advanced type of SQL Injections and they are also fully detectable by Acunetix with AcuMonitor. They are most common in the case of Microsoft SQL Server and Oracle database management systems.

Not Only SQL Injections
Acunetix is not just a tool for SQL Injection testing. It is a complete web application vulnerability scanner that detects an impressive range of security vulnerabilities.
- Acunetix detects many types of Cross-site Scripting (XSS) vulnerabilities. This includes not only stored (persistent) XSS and reflected XSS but also much more advanced DOM-based XSS.
- Some of the other types of vulnerabilities that Acunetix detects are Cross-site Request Forgery (CSRF), directory traversal, and many more. Acunetix security testing researchers constantly keep their fingers on the pulse and new vulnerabilities are added to the detection database regularly.
- In addition to vulnerabilities, Acunetix can also help you assess the general safety of the configuration of your web server. For example, it can alert you about weak passwords, misconfigurations, as well as lack of certain options such as HSTS or Content Security Policy (CSP).
More Than Just Detection
For a business, detection is not enough. You need a solution that is able to help you assess the impact and the severity of vulnerabilities as well as a solution that helps you manage them after they are discovered.
- Acunetix is also a vulnerability assessment tool. Each discovered vulnerability is classified according to renowned classification systems and reported along with information about potential consequences and fixes. Vulnerabilities are also assigned a severity level.
- After detection and assessment, Acunetix also helps you manage the vulnerability further. It works with leading issue trackers and CI/CD systems such as Jira, Jenkins, GitHub, GitLab, and more. This lets you include Acunetix scans early in your SDLC as well as make sure that no vulnerability is forgotten about.
- The Acunetix reporting engine can be used by both developers and managers to deliver reports that fit specific needs. It even has built-in compliance reports for security audits including PCI DSS and HIPAA.
Frequently asked questions
SQL Injections are vulnerabilities in dynamic web sites and web applications that use SQL databases. An SQL Injection lets an attacker get more information about the database, access it, or even completely destroy it or take it over. SQL Injections are considered one of the most dangerous web vulnerabilities.
You can find SQL Injections manually or automatically. To do it manually, you must try different input in web forms, URLs, and other places where the web application might use that input to query a database. To do it automatically, you must run a web vulnerability scanner.
Watch step-by-step how an SQL Injection is discovered manually.
A professional web vulnerability scanner like Acunetix performs SQL Injections in a non-destructive way. As proof, it often provides you with information about the database or information retrieved from the database. It also shows you exactly what input it used, so you can confirm the injection manually.
See the consequences of an SQL Injection that was not detected.
If you develop in PHP, Java, or .NET, you can use AcuSensor to further improve SQL Injection scanning. AcuSensor works together with the back-end interpreter or compiler to pinpoint vulnerabilities in the source code or byte code. Using AcuSensor, you can remediate SQL Injections much faster.
Recommended Reading
Learn more about prominent vulnerabilities, keep up with recent product updates, and catch the latest news from Acunetix.

“We use Acunetix as part of our Security in the SDLC and to test code in DEV and SIT before being promoted to Production.”
Kurt Zanzi, Xerox CA-MMIS Information Securtiy Office, Xerox