Vulnerability management (VM) is the ongoing effort of discovering, measuring, and remediating vulnerabilities. Acunetix has advanced VM features built right into its core, helps prioritize risks based on a single, consolidated view, and allows to integrate scan results into other tools and platforms.
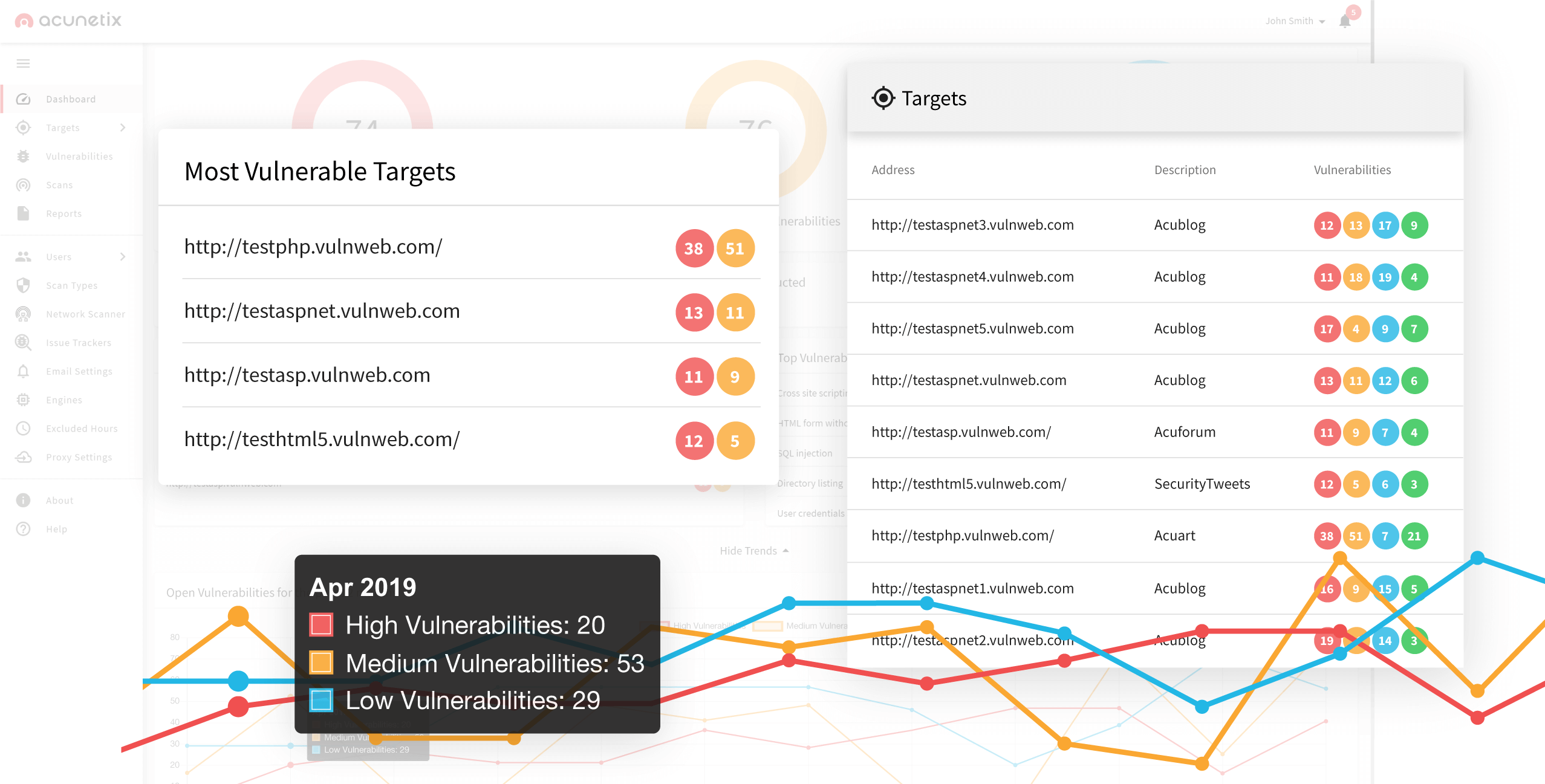
Vulnerability Management in One Consolidated View
It takes teamwork and collaboration to build and maintain an effective security program. The Acunetix multi-user, multi-role features allow your team to be flexible and productive while getting access only to resources they need.- Provides an integrated view of company’s security posture in a single, central location
- Eliminates the need of PDFs and spreadsheets for managing application security
Track Issues, not PDFs
Development teams manage their work loads in issue trackers to fix bugs, track the progress of new features and meet the deadlines. Going to developers with a “300-page PDF” full of security issues that need attention is counterproductive and creates a communication barrier.- Integrates with Atlassian JIRA, GitHub, GitLab, Microsoft Team Foundation Server (TFS), Bugzilla, and Mantis
- Provides management with historical data, trends and prioritization tools
- Reduces time and effort for remediation by integrating into the software development lifecycle
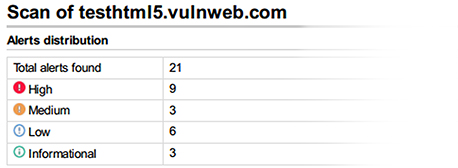
Advanced Management and Compliance Reporting
Acunetix creates reports that allow you to share security findings internally with management and with regulatory bodies. Reports can focus either on a single scan, on a specific target or even on an arbitrary group of scans or targets.- Lets you easily generate detailed technical or management reports
- Includes compliance reports such as PCI DSS, OWASP Top 10, ISO 27001, and HIPAA
Recommended reading
Learn more about prominent vulnerabilities, keep up with recent product updates, and catch the latest news from Acunetix.

“We use Acunetix as part of our Security in the SDLC and to test code in DEV and SIT before being promoted to Production.”
Kurt Zanzi, Xerox CA-MMIS Information Securtiy Office, Xerox