Web Penetration Testing with Acunetix
One of the ways most organizations try to keep up with the onslaught of cybersecurity vulnerabilities is through regular penetration testing (pen testing). Penetration testing is a process in which a skilled penetration tester conducts a series of tests to analyze the attack surface of one or more web applications. Unfortunately, manual web application penetration testing only provides organizations with point-in-time security assessment. Manual penetration tests are also time consuming, expensive, and do not provide a scalable approach to discover critical vulnerabilities such as SQL Injection, Cross-site Scripting (XSS), Local File Inclusion (LFI), and Remote File Inclusion (RFI) – especially when changes to web application source code are made daily.
Continuous Automated Web Application Security Testing
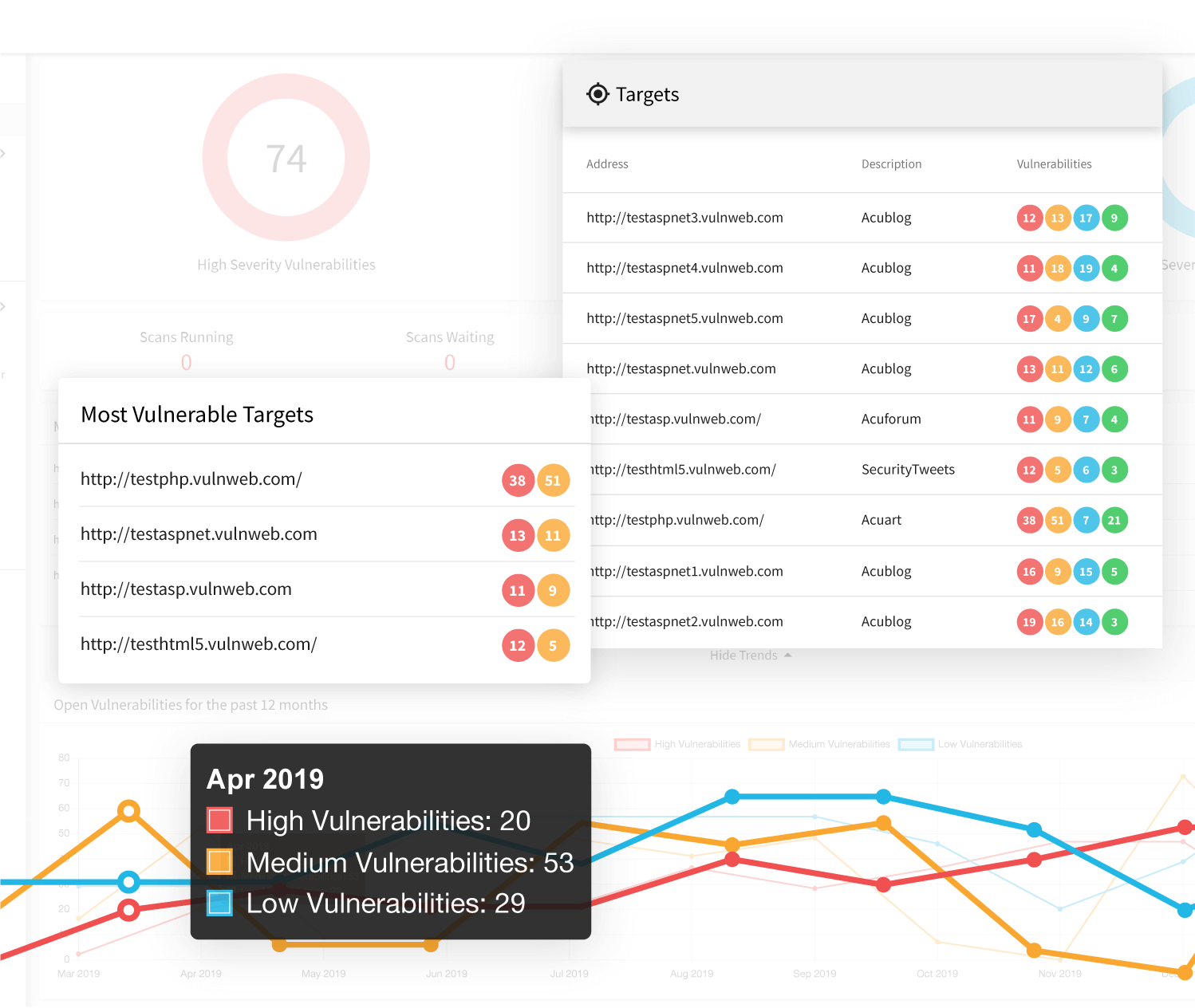
Fortunately, automated web application security tools like Acunetix allow organizations to mimic pentester testing methodologies to find attack vectors in web applications. Acunetix can run both on-demand as well as recurring scheduled scans to cover anywhere from a handful to thousands of web applications quickly, cost effectively, and, most importantly, continuously. While most web vulnerability scanners support legacy technologies, Acunetix has full support for modern JavaScript applications. This means that unlike most web application pentesting software, Acunetix can scan everything that makes part of your software development life cycle – from legacy web applications developed on traditional stacks to leading-edge web apps taking advantage of all the latest and greatest client-side technologies.
Integrate with Other Penetration Testing Solutions and WAFs
Integrations with third-party penetration testing software like PortSwigger Burp Suite and leading web application firewalls (WAFs) make it easy to move between automatic and manual penetration testing for advanced users who need it. Acunetix can also instantly generate a wide variety of technical and regulatory and compliance reports such as PCI DSS, HIPAA, OWASP Top 10, and several others. Additionally, Acunetix allows development teams to stop digging through PDF and HTML reports with out-of-the-box issue tracker integration for Atlassian Jira, GitHub, GitLab, Bugzilla, Mantis, and Microsoft Team Foundation Server (TFS).
Frequently asked questions
Automated penetration testing is also called vulnerability scanning. A tool for automated web penetration testing, also called a DAST tool (Dynamic Application Security Testing), for example, Acunetix Online, automates many tests that a human penetration tester would otherwise have to perform manually.
Learn about the difference between penetration testing and vulnerability scanning.
There are different types of tools that a security researcher may use for web application penetration testing. Many of them are manual tools but some professional security researchers use automated vulnerability scanners such as Acunetix Online, too.
Online automated penetration testing using a cloud-based web vulnerability scanner such as Acunetix Online is the first and most important step of verifying the security of your website or web application. Some businesses perform additional manual penetration testing to confirm vulnerabilities and find problems that cannot be discovered automatically.
Learn more about how to balance automatic and manual penetration testing for your business.
Automated gray box web application penetration testing means that the tool tests the application the way that a penetration tester would and at the same time it is aware of what is happening on the back-end side. It is also often called Interactive Application Security Testing (IAST).
Recommended Reading
Learn more about prominent vulnerabilities, keep up with recent product updates, and catch the latest news from Acunetix.

“We use Acunetix as part of our Security in the SDLC and to test code in DEV and SIT before being promoted to Production.”
Kurt Zanzi, Xerox CA-MMIS Information Securtiy Office, Xerox