Beyond Low-Hanging Fruit
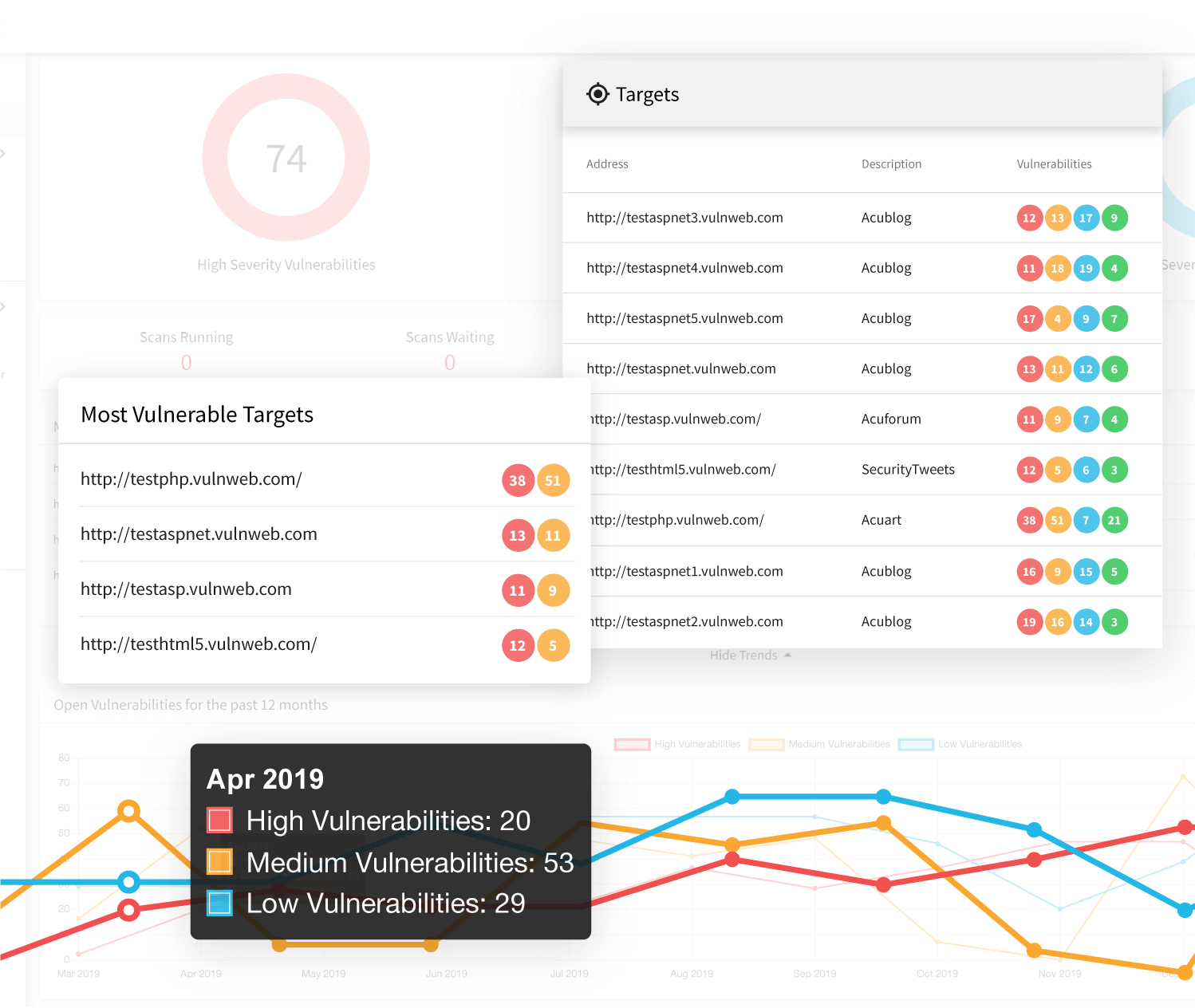
While many web vulnerability scanners can find low-hanging XXE, Acunetix goes well beyond the basics thanks to its advanced crawler and JavaScript engine called DeepScan. Thanks to DeepScan, Acunetix also has full support for modern single-page applications (SPAs) and can understand and fully test applications that rely on JavaScript frameworks like React, Angular, Ember, and Vue. This means that Acunetix can understand an underpinning RESTful API when crawling a SPA. Since Acunetix can not just understand JSON and XML, it can build a correct input scheme (an internal representation of web application input), which it may then rigorously test for XXE and other attacks such as SQL Injection, Cross-site Scripting (XSS), and HTTP host header attacks.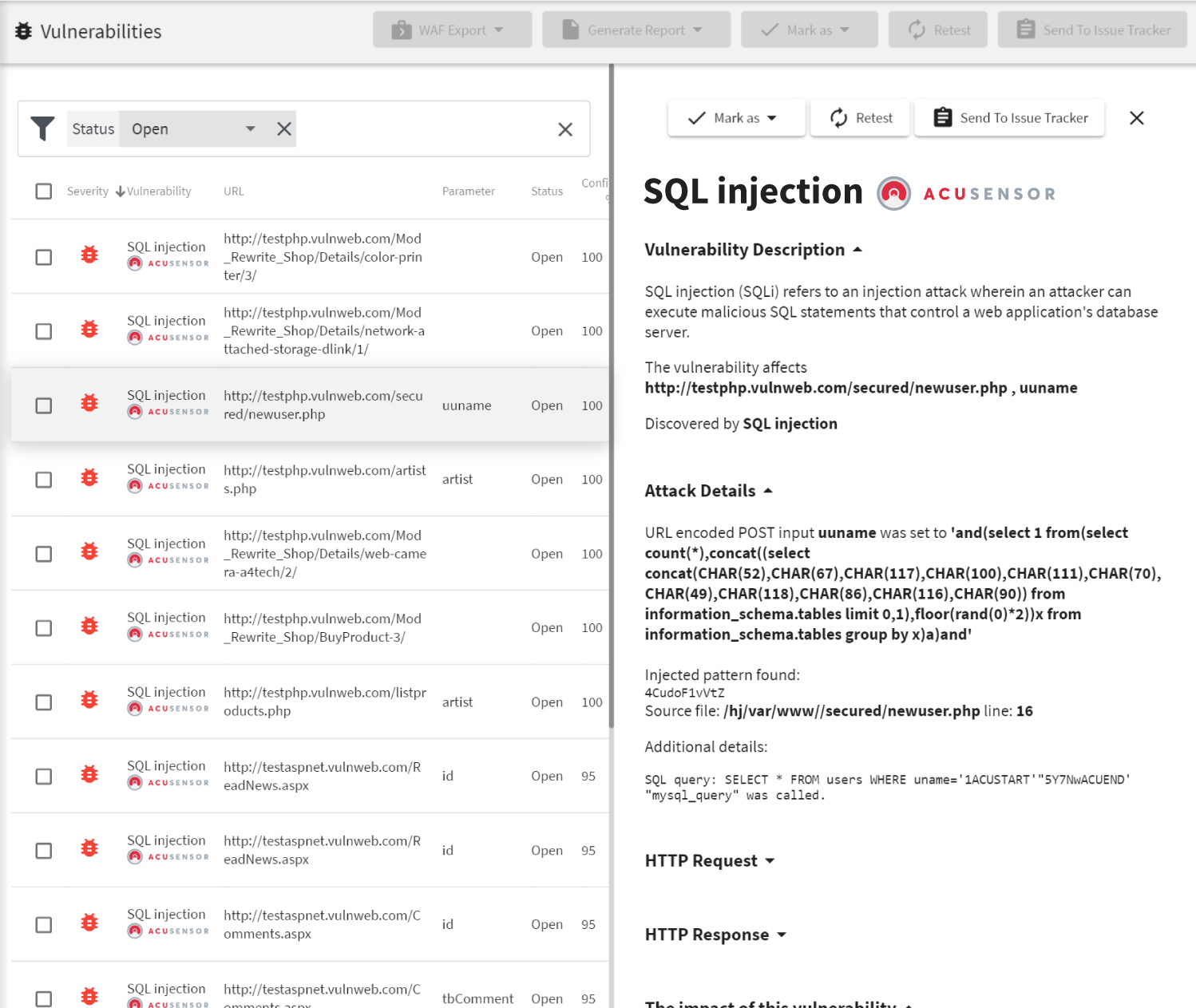
Runtime Source Code Analysis
In addition to being a fully automated black box (no knowledge of backend code) vulnerability scanner, Acunetix also provides AcuSensor as part of its standard offering. AcuSensor is a an optional sensor for Java, ASP.NET, and PHP applications that can easily be deployed on the application backend to analyze source code while it is in execution by the scanner. This type of testing is known as gray box testing since it combines the best of both worlds from black box testing and white box testing. When testing for XXE vulnerabilities, Acunetix AcuSensor increases the accuracy of a scan since it has access to the code on the backend. With AcuSensor, the Acunetix vulnerability scanner may also test pages that would not otherwise be discovered via crawling thanks to the AcuSensor backend crawl technology.Frequently asked questions
XXE (XML external entity) is a class of vulnerabilities in web applications and attacks that exploit these vulnerabilities. XXE vulnerabilities allow the attacker to inject XML code into the application through regular user input. This XML code is then processed by the web application with potentially dangerous results.
XXE can lead to denial-of-service attacks, theft of information, and even to other attacks such as SSRF (server-side request forgery) or RCE (remote code execution). Therefore, it can be very dangerous.
See how an attacker can steal confidential information using XXE.
The only way to check if you have XXE issues is to use a vulnerability scanner. Several scanners are able to detect this type of attack but Acunetix is one of the very few that can also prove it. This means that Acunetix will, for example, show you that it accessed a confidential file from your web application using XXE.
Recommended reading
Learn more about prominent vulnerabilities, keep up with recent product updates, and catch the latest news from Acunetix.

“We use Acunetix as part of our Security in the SDLC and to test code in DEV and SIT before being promoted to Production.”
Kurt Zanzi, Xerox CA-MMIS Information Securtiy Office, Xerox