Recently over 100,000 Apple customers were affected by an information disclosure attack on the AT&T website. Security experts blame this breach on “poorly designed software”. An analysis of the attack reveals that the hackers did indeed use a classic PHP attack, in fact the only tool used in this breach was a PHP script that enumerated all ICC-ID numbers, and launched an HTTP GET request for each ID. If an ID matched an Apple iPad subscriber, his or her email address was revealed.
Recently over 100,000 Apple customers were affected by an information disclosure attack on the AT&T website. Security experts blame this breach on “poorly designed software”. An analysis of the attack reveals that the hackers did indeed use a classic PHP attack, in fact the only tool used in this breach was a PHP script that enumerated all ICC-ID numbers, and launched an HTTP GET request for each ID. If an ID matched an Apple iPad subscriber, his or her email address was revealed.
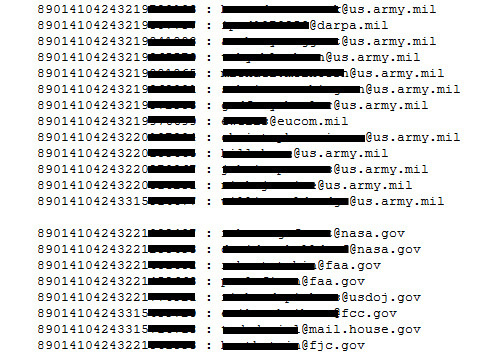
The image below shows just a snippet of the information harvested by the attackers. You will notice that in this list exist many US Military and Government email addresses. This begs the question; why are users of the US Whitehouse, DARPA and army using their government email address for their iPhone subscriptions?
LEARN MORE: How to Prevent SQL Injection in PHP
The flaw in detail
The mistake in the AT&T website software was subtle, but the results were very damaging. At the core of problem lies in a script on the AT&T website: https://dcp2.att.com/OEPClient/openPage
This script takes one parameter called “ICCID” and another, which apparently is ignored called “IMEI”. If a valid ICCID is passed, the script will respond with the email address of the ICCD subscriber. For those wondering, the ICC-ID stands for Integrated Circuit Card Identifier. It is a number that associates a SIM card with a subscriber, so every iPhone and iPad user has one. If you have an iPhone or IPad, you can find your ICC-ID number from the About screen as shown in the image below.
The script will be invoked remotely using a standard HTTP GET request, that will look something like this: https://dcp2.att.com/OEPClient/openPage?ICCID=89014103211479197174&IMEI=0
This request is legitimate, and therefore was not detected by AT&T when the breach occurred, allowing the hackers to harvest a huge number of email addresses before they announced the hack to the world.
The attack script
Goatse Security, the group behind this exploit revealed the PHP script that they used. This allowed security researchers to peek ‘behind the scenes’ and see what techniques were used. Below is the script, titled “iPad 3G Account Slurper”. I bolded the sections I found interesting, and which I will explain further down.
Click on script to enlarge image
This script is not a work of art (like most PHP code out there), but it does the trick. Here are the portions I find most significant.
$useragent=”Mozilla/5.0 (iPad)”; //Spoof as iPad
The line above sets the HTTP User-Agent header to the one that the iPad uses. This makes the AT&T website believe that the request came from an iPad. Generally, its a bad idea for web applications to rely on the user agent because this field can be spoofed very easily.
while (1) { //Continue FOREVER
This line instructs the script to keep running forever, or until a human turns it off. During this hack it was allowed to run at least 100,000 times, however there is no limit to how many email addresses could be harvested. This line also shows the programmer’s confidence in the fact that his attack cannot be detected, especially if he uses proxies to continuously change his IP address (another common technique used to avoid detection due to too much traffic from one source IP.)
$ICCID = $ICCIDroot.genluhn(strval($ICCIDroot)); //Generate checkdigit and attach it to the ICCID
This line creates a new ICC-ID, which will be used later. The ICC-ID has something called a “Check Digit”. This is a number derived and appended to the ICC-ID itself, and was supposedly created to detect ICC-ID corruption and to minimize spoofing. With a touch of ingenuity the programmer includes an algorithm in his script that re-generates the check digit for every ICC-ID attempted. This ensures the integrity and validity of the ICC-IDs he spoofs.
curl_setopt($ch, CURLOPT_URL, “https://dcp2.att.com/OEPClient/
openPage?ICCID=”.strval($ICCID).”&IMEI=0″);
This line is the ‘core’ of the script, and is the one that crafts the URL that will be used to harvest email addresses. It is strange to me, that the IMEI is always set to 0. I am only speculating, but it might have been possible to avoid or seriously thwart this attack if the IMEI associated with the ICC-ID was validated.
if (preg_match(“<input id=”email” name=”email” type=”email”
placeholder=”Required” value=”.*@.*” autocapitalization=”off”
autocorrect=”off”>”,
$output, $match)) {
The line above is a very crude (I repeat, very crude) way of parsing out the email address from the served HTML. It uses the powerful regular expression library (RegEx) in a very loose way, however it seems that it did the trick for the hacker. It does indicate, however that the script was written in a hurry.
Preventing this type of attack
This attack does not exploit and XSS (Cross Site Scripting), SQL Injection or CRLF injection techniques. In fact, looking at the PHP script reveals that the attack would have been impossible to detect, even if a Web Application Firewall was used. This type of attack can only be prevented by implementing proper quality controls.
LEARN MORE: How to Prevent SQL Injection in PHP
Get the latest content on web security
in your inbox each week.