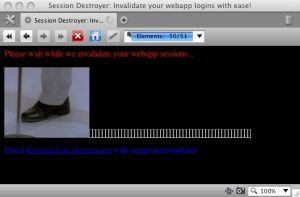
A recent post on “Full-Disclosure” mailing list referenced a web page called “Session Destroyer”. This web page is a demonstration by Kristian Erik Hermansen that promises to make logging off various popular websites very easy.
How does it work? This static html page simply contains IMG tags that link to the logout url for various websites including Facebook, Gmail, Ebay, Youtube and Yahoo. If an unwary user visit this web page then he or she will instantly get logged out of these popular websites. While this is a nuisance, it is not considered a serious security hole and knowledge of this issue is widespread throughout the security community.
In fact this sort of issue has a name – Cross Site Request Forgery or CSRF / XSRF, and can have very serious repurcussions. This security flaw relies on the fact that web browsers will happily go to any URL that is referenced by any website, even if the URL refers to a totally different website. If the URL performs an action, (eg. logs out the user or transfers some money to another bank account) AND the URL’s parameters are predictable, then that web application is typically vulnerable to a CSRF attack. Major sites such as Gmail were previously found to be vulnerable to CSRF. In the case of Gmail, attackers were able to add an email filter that forwarded the victim’s emails to their own email address.
To solve this issue, web developers usually create a secret that the attacker cannot predict and that is known between the web application and the legitimate user. Making use of POST requests is not a solution to CSRF since attackers can force web browsers to submit forms. The solution is to make use of a challenge token for each request – or at least those requests that execute a sensitive action.
Get the latest content on web security
in your inbox each week.