 Among many advanced penetration testing tools provided, Acunetix Web Vulnerability Scanner (WVS) offers you the HTTP Sniffer tool. With the HTTP Sniffer you can capture, trap, analyze and even modify any HTTP traffic that the sniffer is listening to, e.g. port 8080. The Acunetix HTTP Sniffer is a combination of a proxy server and a sniffer. This gives the ability to the scanner to sniff any HTTP requests and responses between a web client and a web server. Therefore you have the opportunity to control and gain more information about the HTTP requests and responses, as well as their values and their behavior in real-time.
Among many advanced penetration testing tools provided, Acunetix Web Vulnerability Scanner (WVS) offers you the HTTP Sniffer tool. With the HTTP Sniffer you can capture, trap, analyze and even modify any HTTP traffic that the sniffer is listening to, e.g. port 8080. The Acunetix HTTP Sniffer is a combination of a proxy server and a sniffer. This gives the ability to the scanner to sniff any HTTP requests and responses between a web client and a web server. Therefore you have the opportunity to control and gain more information about the HTTP requests and responses, as well as their values and their behavior in real-time.
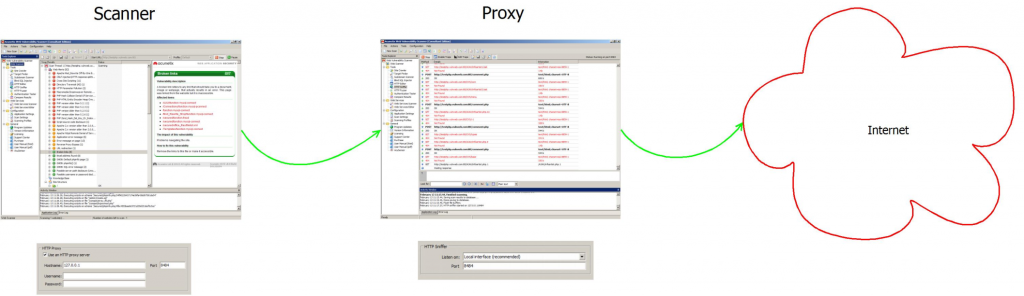
Acunetix WVS can also be configured to send traffic through a proxy server. As a result, you can use the Acunetix WVS as a proxy to monitor activity of another Acunetix WVS instance.
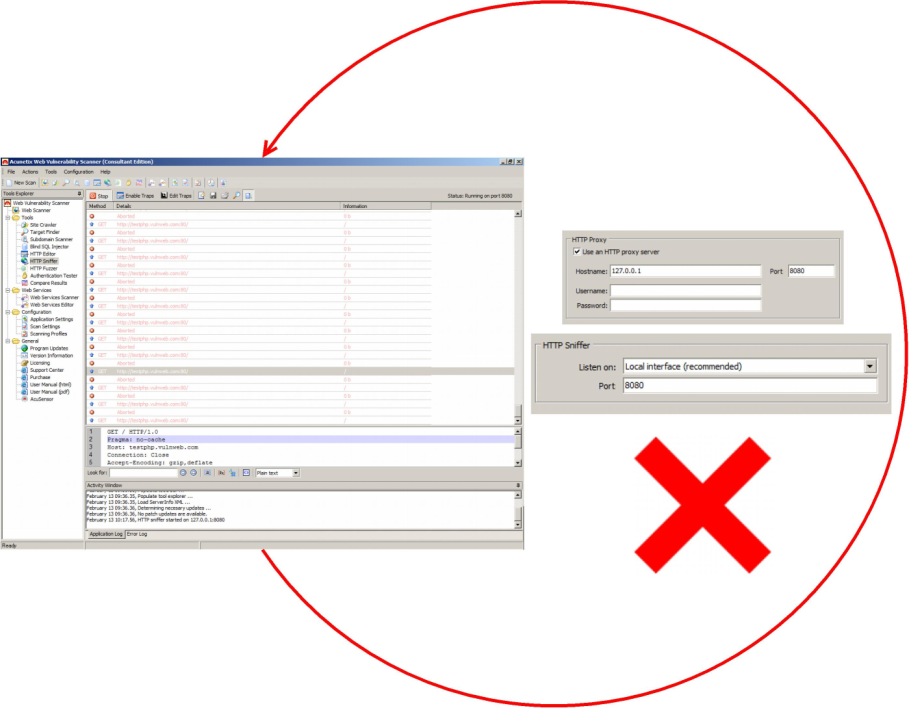
These two features (Acunetix WVS acting as a proxy and also forward traffic to a proxy) should never be configured to operate on the same port if their target interface is the same, because Acunetix WVS sends HTTP traffic through the configured proxy server, for example port 8080, and the HTTP Sniffer listens to the traffic from port 8080. This will result in receiving its own traffic back.
The above example shows how Acunetix HTTP Sniffer could be wrongly configured to send the traffic back to itself.
The above image includes a Acunetix WVS instance that performs a scan and another instance of Acunetix WVS that acts as a sniffer/proxy. The first instance (”Scanner”) has the HTTP Proxy Settings configured to pass traffic through the port 8484. The second instance (”Proxy”) has the HTTP Sniffer settings configured to port 8484. The second instance (”Proxy”) will listen to any HTTP traffic that is sent by the first instance (”Scanner”) and subsequently will pass the traffic to the internet. Therefore, the traffic is not trapped in a loop. The second instance that is been used as a proxy receives the HTTP traffic from the first instance used as a scanner and consequently the traffic is sent successfully to the Internet.
To receive updates about the Acunetix WVS and the latest web security news like the Acunetix Facebook Page and read the Acunetix Blog. Also follow us on Twitter.
Get the latest content on web security
in your inbox each week.