The WordPress database is the most important component of your WordPress website. It contains all the content of your website, such as information about your users and all your posts, etc.
The WordPress database is the most important component of your WordPress website. It contains all the content of your website, such as information about your users and all your posts, etc.
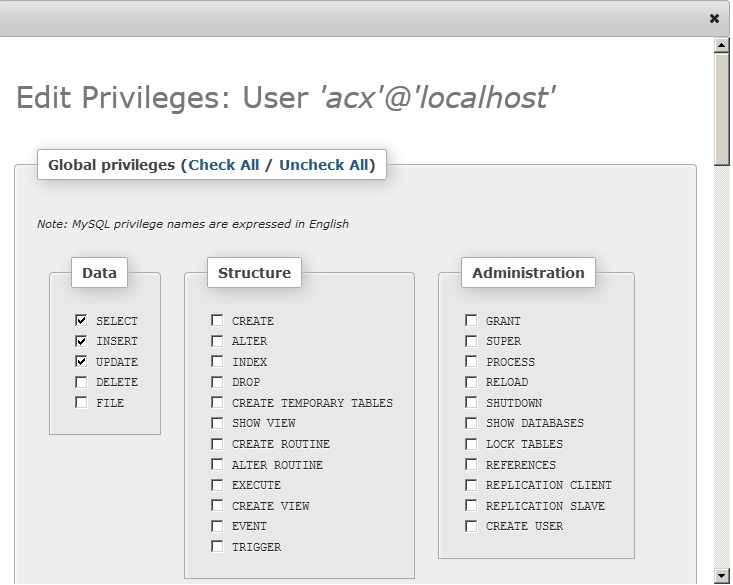
In order to access the database, a database user should have specific privileges that allow him or her to manipulate it. The WordPress database is built using MySQL and contains privileges which allow users to make certain changes. The ‘grant access privileges’ give users full privileges. This is a very convenient option for a user if they want to have full control over the WordPress database.
However, from the security point of view, this is extremely dangerous, since if a hacker gains access to the database then he or she will have full control over the WordPress database and the stored data, which can have catastrophic consequences on your website security. Therefore it’s not recommended to grant a user full access, unless the user needs to be able to use the DROP or DELETE SQL commands.
Below is an example of the minimum privileges a database user needs to have. Other database permissions are regarded as “extra” privileges that in most cases are not needed. A typical WordPress user should be granted the following database privileges only:
- SELECT
- INSERT
- UPDATE
If you are upgrading WordPress, the above database permissions might not suffice between versions, WordPress might need to make further changes to the database. In this case, if you are only upgrading to the latest version of WordPress, add the below privileges to the WordPress database user:
- CREATE
- ALTER
NOTE: Some plugins might require additional database privileges such as CREATE, DROP or DELETE and in those cases these privileges should be granted.
In addition to securing your WordPress database permissions, you should make sure that each database of your website is accessed through a separate account and not through the root account. Read our article on why you shouldn’t access your WordPress databases using the root account.
Get the latest content on web security
in your inbox each week.