Scan SQL Injection Online with Acunetix SQL Injection Scanner
SQL Injection (SQLi) is an attack in which an attacker can execute malicious SQL payloads or statements that allows them to control a web application’s database server (such as MySQL, Microsoft SQL Server, and Oracle) through regular HTTP requests. SQL Injection attacks are a major cause for concern within web applications since they are both a popular hacker target and typically easy to exploit using automated testing tools. Successful exploitation is likely to lead to full-scale data breaches, and once an attacker succeeds at SQL Injection, it becomes much easier for them to take advantage of other critical vulnerabilities to escalate their attack further. SQL Injection vulnerabilities are usually not difficult to fix, but finding them in large codebases could be challenging without the right tools. Acunetix is a web application vulnerability scanner and as part of the myriad of vulnerability test it performs, SQL Injection is certainly one of them.
Comprehensive SQL Injection Test Online
The Acunetix SQL Injection scanner tests for a wide variety of SQL Injection, including error-based, blind SQLi, and even out-of-band SQLi. While many website security scanners can find low-hanging fruit, Acunetix goes well beyond the basics thanks to its advanced crawler and JavaScript engine called DeepScan. Thanks to DeepScan, Acunetix also has full support for modern single-page applications (SPAs) and can understand and fully test target websites that rely on JavaScript frameworks like React, Angular, Ember, and Vue. This means Acunetix can understand a RESTful API when crawling a SPA. Since Acunetix can understand JSON and XML, it can build a correct input scheme (an internal representation of web application input), which it may then rigorously test for SQL Injection and other vulnerabilities such as Cross-site Scripting (XSS), HTTP host header attacks, and other web vulnerabilities. Furthermore, Acunetix can also scan for vulnerable open-source JavaScipt libraries, as well as security vulnerabilities and misconfigurations within web servers, SSL/TLS, and CMS software such as WordPress, Drupal, and Joomla – all with the lowest false positive rate in the industry.
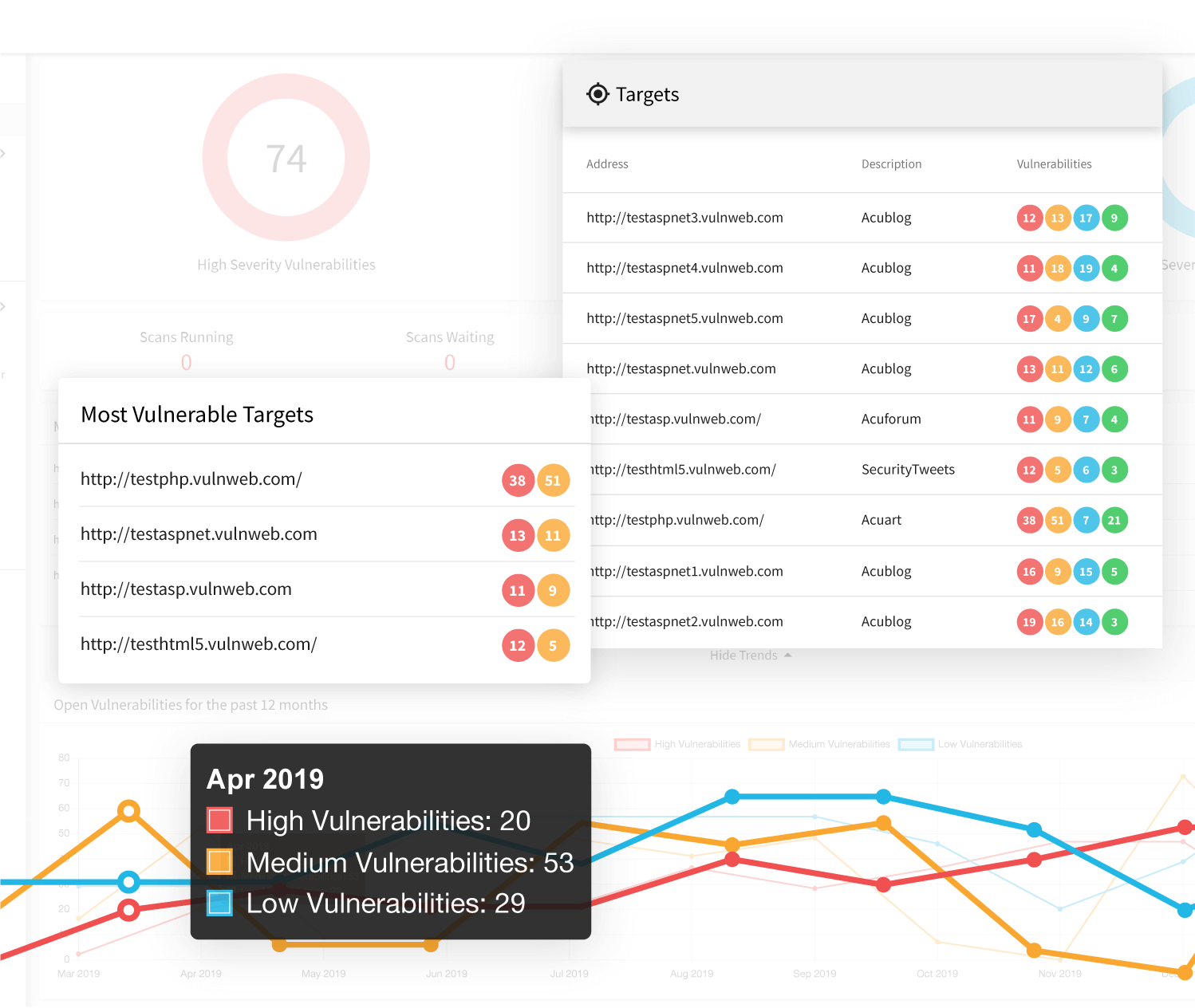
Out-of-the-Box SQL Injectoin Scan Reporting and Issue Tracker Integration
It’s no secret that for most security professionals reporting is a burden and a takes up an enormous amount of time. Acunetix allows you to instantly generate a wide variety of comprehensive reports such as PCI DSS, HIPAA, OWASP Top 10, and many others. Additionally, Acunetix allows users to export discovered vulnerabilities to issue trackers such as Atlassian Jira, GitHub, GitLab, Microsoft TFS, Bugzilla, and Mantis, as well as export scan results to popular web application firewalls to be virtually patched automatically, so both security teams and developers can have clear scan reports regardless of the tools they organize their work in, allowing them to stay in sync without the need to switch tools or sift through PDFs.
Frequently asked questions
The best way to test for SQL Injection vulnerabilities and other web vulnerabilities is to use a renowned vulnerability scanner. The Acunetix vulnerability scanner is considered a market leader in web vulnerability scanning and vulnerability management.
To check for SQL Injection, Acunetix Online attempts to inject SQL into your website or web application in a harmless way. For example, Acunetix may use an SQL Injection to show you a version of your database software, which should not be visible from the outside.
SQL Injections are considered one of the most dangerous web vulnerabilities because they often let the attacker take full control of the database. An attacker may then use privilege escalation to take over the whole system.
See an example of how an SQL Injection attack may lead to full system compromise.
An online solution is just as effective in checking for SQL Injections as an on-premises solution. There are several advantages of a cloud solution, for example, no local resource consumption.
See how to scan non-public websites and web applications for SQL Injections using Acunetix Online.
Recommended Reading
Learn more about prominent vulnerabilities, keep up with recent product updates, and catch the latest news from Acunetix.

“We use Acunetix as part of our Security in the SDLC and to test code in DEV and SIT before being promoted to Production.”
Kurt Zanzi, Xerox CA-MMIS Information Securtiy Office, Xerox