If you are not an expert in web application security, you may find it difficult to figure out what you can do to make sure that your websites and web applications are safe from malicious hackers. Here are some basic facts about web app security and some cybersecurity-related recommendations for you.
Why Are My Web Assets in Danger?
Websites and web applications are the most vulnerable business asset because they are most often available publicly. For example, your internal company network is not very vulnerable because you can use a firewall to block access to your resources. However, you cannot block access to your website or web app, so everyone can try to hack it.- Most security vulnerabilities in web apps are caused by programmer errors. Web application security vulnerabilities such as SQL Injections, Cross-site Scripting (XSS), or Cross-site Request Forgery (CSRF) may be leveraged by the attacker as attack vectors to either access your sensitive data, compromise your web server, or endanger your users.
- Web application vulnerabilities appear not only in your own web applications but even more often in popular open-source or commercial products. For example, new WordPress security threats appear almost every other week and affect everyone who uses WordPress and its plugins.
- Most companies are unaware of the importance of web security. They focus on protecting their end-user computers using anti-malware tools and their internal networks using network security solutions. However, they leave key entry points completely open because they think that they are not going to become victims of a web application attack, and they are wrong. Web vulnerabilities and misconfigurations are causes of the biggest data breaches.
How Can I Protect My Web Assets?
Complex security offerings do not protect your web assets at all. If you buy a complex solution, even from the best manufacturers, they will protect only part of your systems. You need specialized software to protect your websites and guarantee web app security.- Web application firewall (WAF) manufacturers may tell you that their software will protect your website and web application, but it will not. WAFs are like band-aids – they make it difficult for attackers to hack you, but not impossible. You need to eliminate the root of the problem – the vulnerability.
- Many network security products claim to have tests for web vulnerabilities but they only cover the most popular and easiest to discover cases and they report a lot of false positives (false alarms). They treat network security as their primary focus and therefore cannot provide you with truly effective web security measures.
- The best way to discover web application vulnerabilities would be to have security professionals who manually test every website and web application – this is called penetration testing. Unfortunately, this is practically impossible because penetration testing takes a lot of time, it is very costly, and there are not enough such professionals available. Therefore, you must help them with an automated solution that discovers most vulnerabilities, leaving only the most complex ones to the pros.

How Do I Use a Web Vulnerability Scanner?
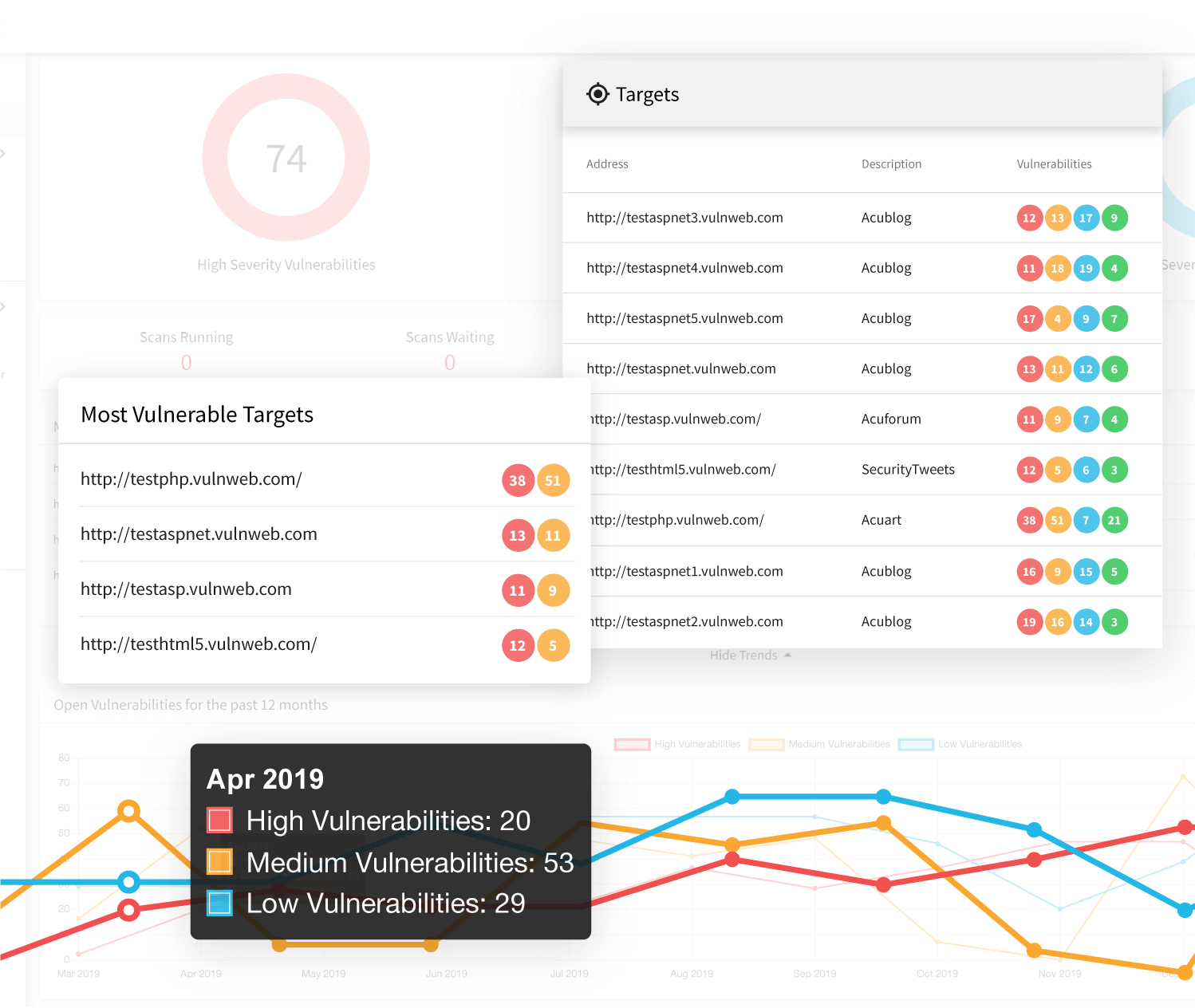
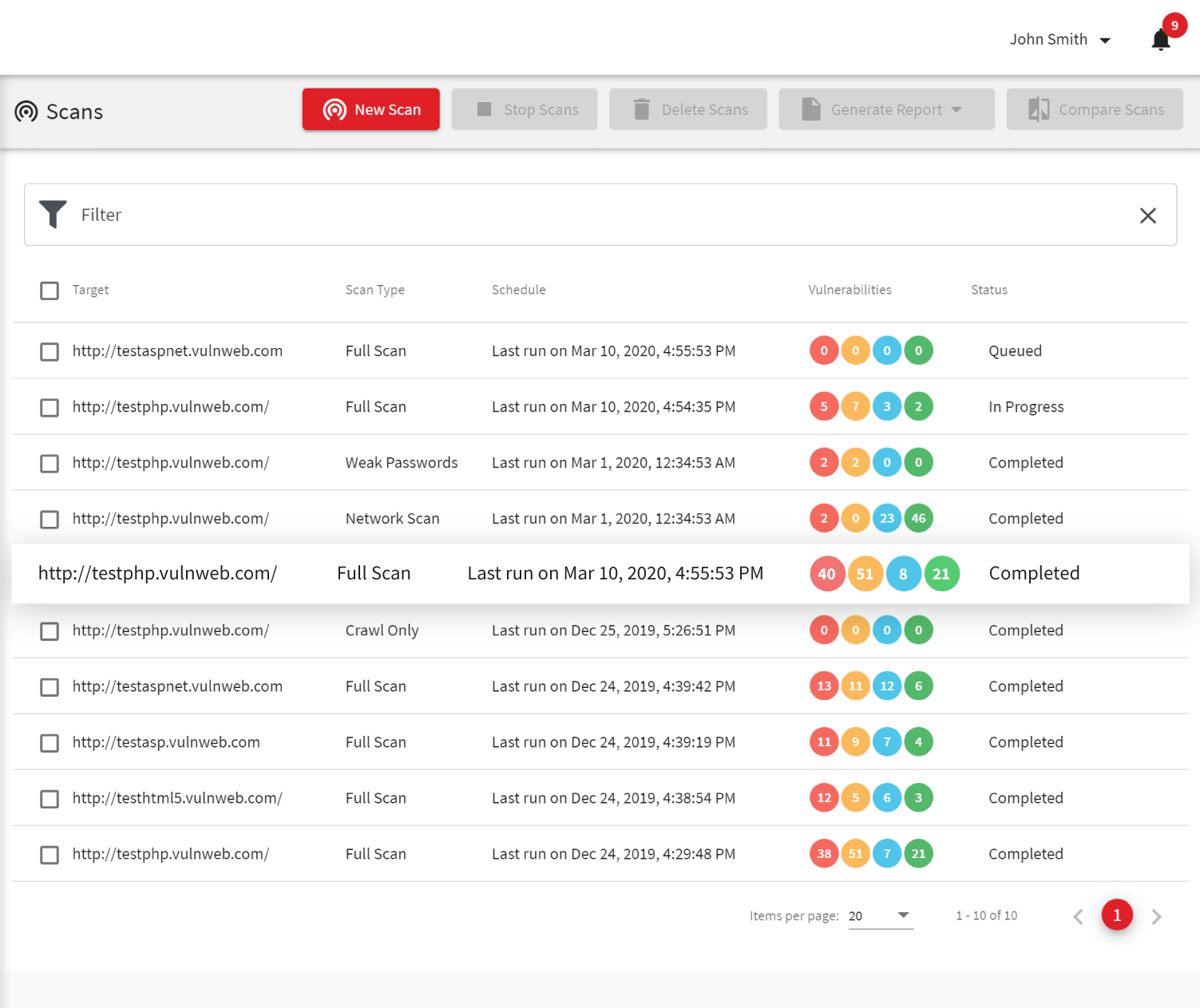
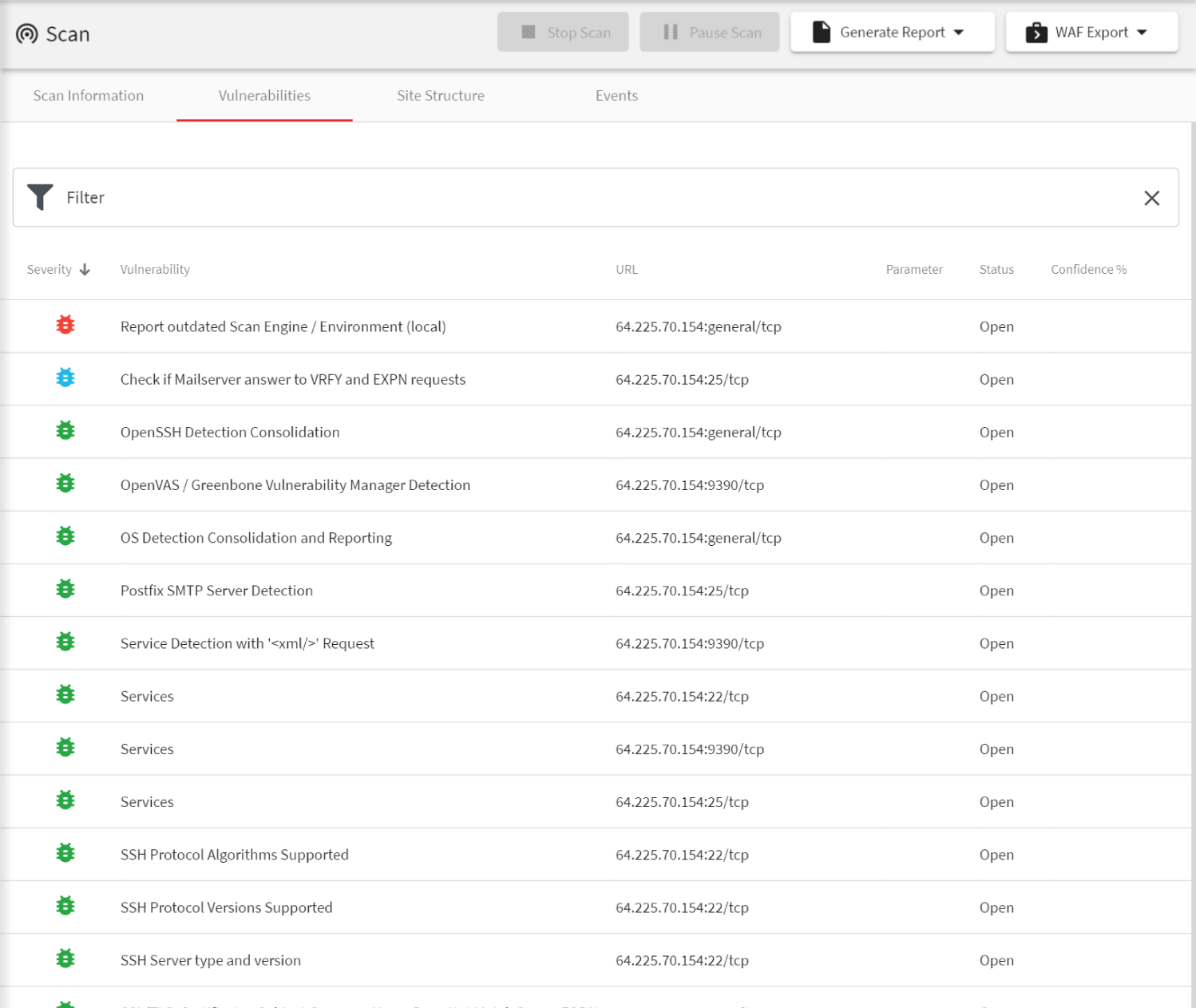
The only type of software that can help you secure web assets is a web vulnerability scanner. This type of software checks your websites and web applications for security issues from the client-side and does not need access to the source code at all. There are very few professional tools that can do that and Acunetix is one of the very few that can not only find the vulnerabilities but prove them and provide you with exact details on how to fix them.- At first, you should schedule regular scans for all your websites and web applications. We recommend that you scan your staging servers rather than your production servers but you can do both. You can schedule complete scans every week and then high-priority and/or incremental scans every day.
- If your company develops web applications, it is best to include web application security testing as part of your software development lifecycle (SDLC). For example, you can install a Jenkins plugin so that Acunetix automatically scans every build of your application. You can also integrate Acunetix with Jira, GitHub, GitLab or similar software so that an issue is automatically created when a vulnerability is found.
- Once your vulnerability scanner identifies the majority of security issues in your websites and web applications, you may want to make sure that you are even better protected. What you can do is export results directly to a web application firewall and temporarily block most attack attempts while all the vulnerabilities are fixed. You may also hire penetration testing experts to further analyze your web assets for vulnerabilities that automated scanners cannot find, for example, business logic vulnerabilities.
Why Acunetix?
Now that you know that you must have a web vulnerability scanner to protect your web assets and sensitive information, you may ask why choose Acunetix in particular? Here are some of the reasons why we believe that our product is the best.- We have the most experience of all manufacturers. Acunetix is the oldest security tool developed continuously by the same team for over 15 years. We focus completely on web security and we believe that this is the best approach to provide a product, which outclasses any others on the market. We are also the only one on Linux, Windows, macOS, and available as a cloud service.
- We believe that web application security is the most important area of security for businesses. The web is everywhere! Most services move to the cloud and many technologies (e.g. mobile apps and the Internet of Things) use web services. However, we also provide network security and anti-malware integration as part of our solution so that your web server is fully protected.
- We are very proud to be used by both small companies as well as huge enterprises and even white-hat hackers. This proves that our product can fulfill many needs and help everyone eliminate security risks associated with the web application layer.
Recommended reading
Learn more about prominent vulnerabilities, keep up with recent product updates, and catch the latest news from Acunetix.

“We use Acunetix as part of our Security in the SDLC and to test code in DEV and SIT before being promoted to Production.”
Kurt Zanzi, Xerox CA-MMIS Information Securtiy Office, Xerox