The multinational financial services corporation MasterCard has become one of the first hacking victims of 2013. The attack was performed by the Syrian Electronic Army who managed to submit a blog post with the title “Hacked By Syrian Electronic Army” after breaching the security of MasterCard’s website.
According to Mohit Kumar, Founder of the thehackernews.com blog website, MasterCard’s Blog was using an outdated version of WordPress. This information could be found by accessing a standard informational file of WordPress – readme.html.
The particular file exists in the root of a WordPress website and contains important information about the WordPress website, such as the version it is using.

This information is useful for an attacker since the attacker can identify if the target WordPress website is up-to-date or not, and exploit known weaknesses.
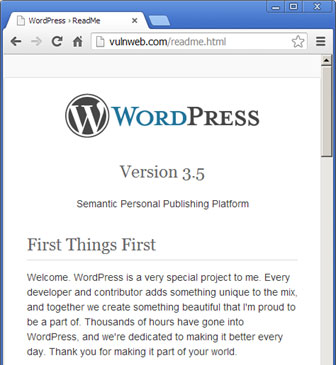
In this scenario it seems that MasterCard’s WordPress website was using version 3.3.2 – an outdated version that includes serious security vulnerabilities such as Cross-Site Scripting, File Upload and Cross-Site Request Forgery.
Thus an attacker using the readme.html file could gain the version information, identify any vulnerability that might exist for the particular version of WordPress and proceed to make further attacks that compromise the security of the website.
The attack on MasterCard is a perfect example to make us aware that if you have a website, you need to take care of online security. It is very good practice to scan your WordPress site for vulnerabilities. Acunetix Online Vulnerability Scanner can assess your WordPress site for vulnerabilities, and will warn you when you are using older versions of WordPress and older versions of WordPress plugins.
Register today to your Acunetix Online Vulnerability Scanner 14-day Trial.
Reference: http://thehackernews.com/2013/01/outdated-version-of-wordpress-leads-to.html
Get the latest content on web security
in your inbox each week.



