Industry Leading Technology Coverage
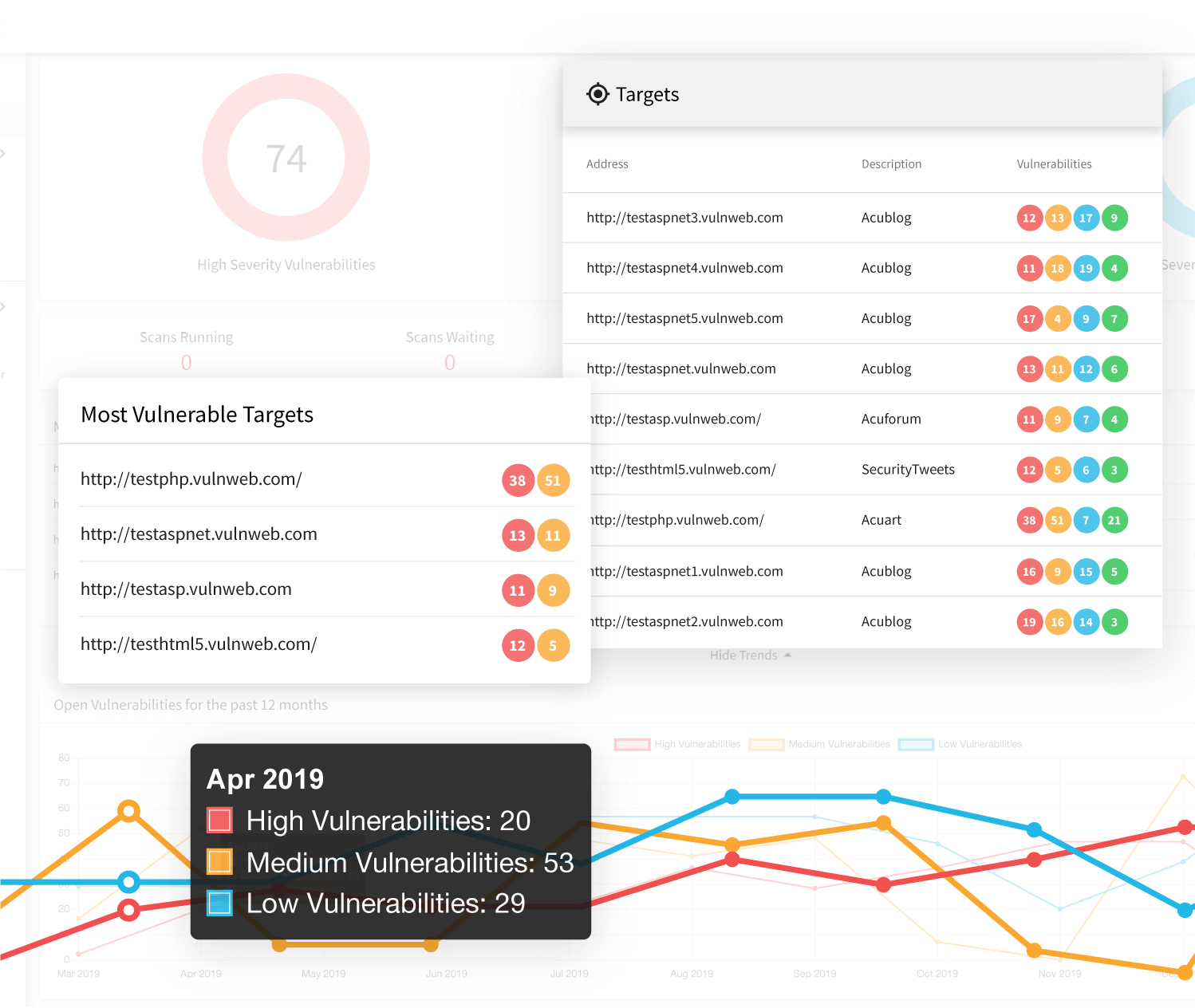
With Acunetix, security teams can setup scheduled automated black-box scans, to test for thousands of web application vulnerabilities and web server misconfigurations. While most black-box security testing tools support legacy technologies, Acunetix takes technology support to the next level with the best-of-breed JavaScript support. Unlike most black-box testing tools, Acunetix has full support for modern Single Page Applications (SPAs) and can understand and fully test applications which rely on JavaScript frameworks like React, Angular, Ember and Vue. This means that unlike most automated scanners, Acunetix can scan everything from legacy web applications developed on traditional stacks, as well as modern web apps taking advantage of all the latest and greatest technologies without sacrificing accuracy and keeping its false-positive rate near zero.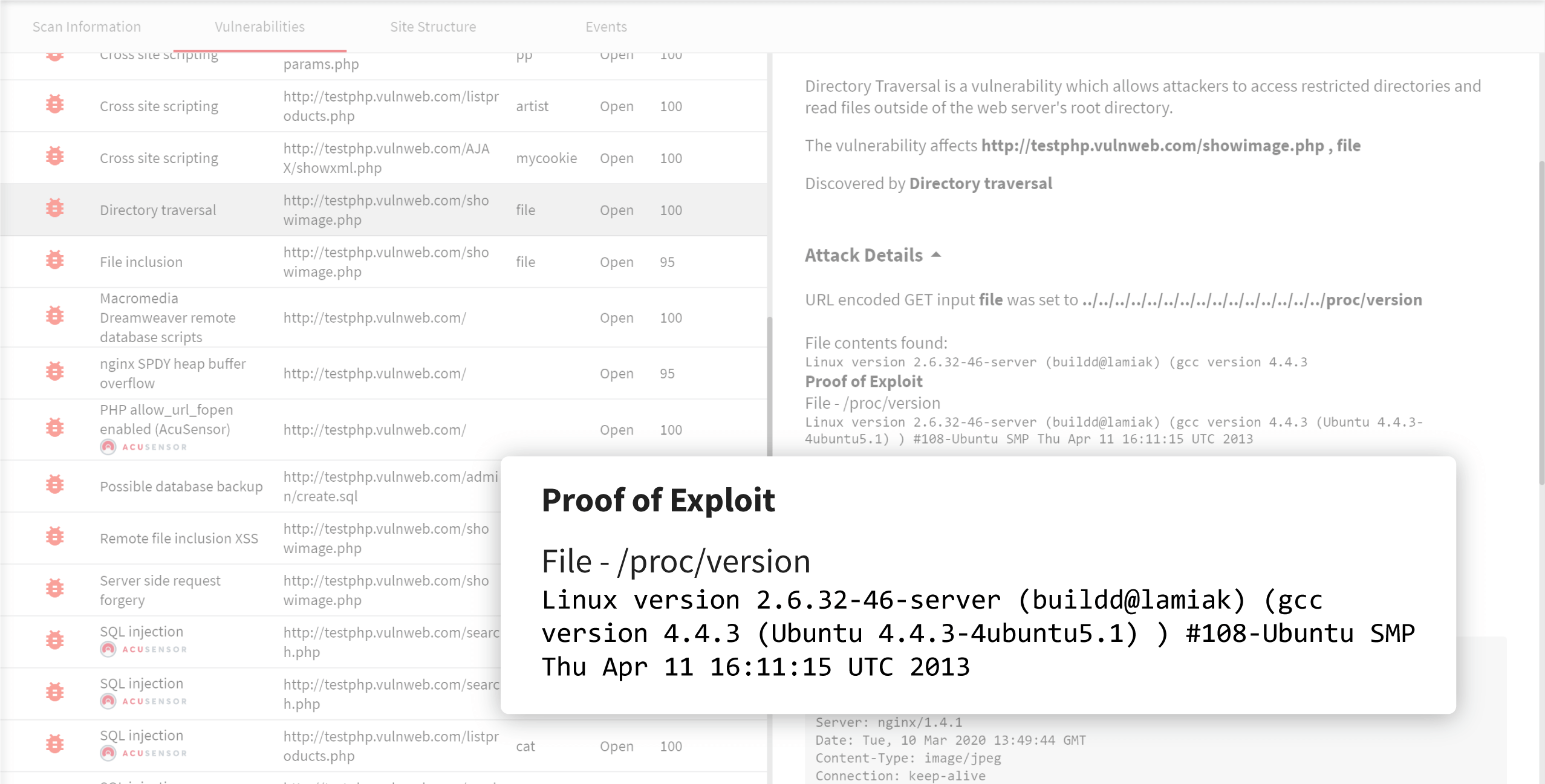
Speed without sacrificing flexibility
Additionally, unlike many other external vulnerability scanners, Acunetix is lightning fast. With a re-engineered core, and a highly optimized crawler, every inch of Acunetix is tuned for speed and efficiency, allowing it to scan hundreds of thousands of web pages without breaking a sweat. What’s more, Acunetix can save the progress of a scan mid way, pause it, and resume it later on from where it left off entirely automatically. This is a crucial for time boxed testing or when scanning enormous web applications with time restrictions.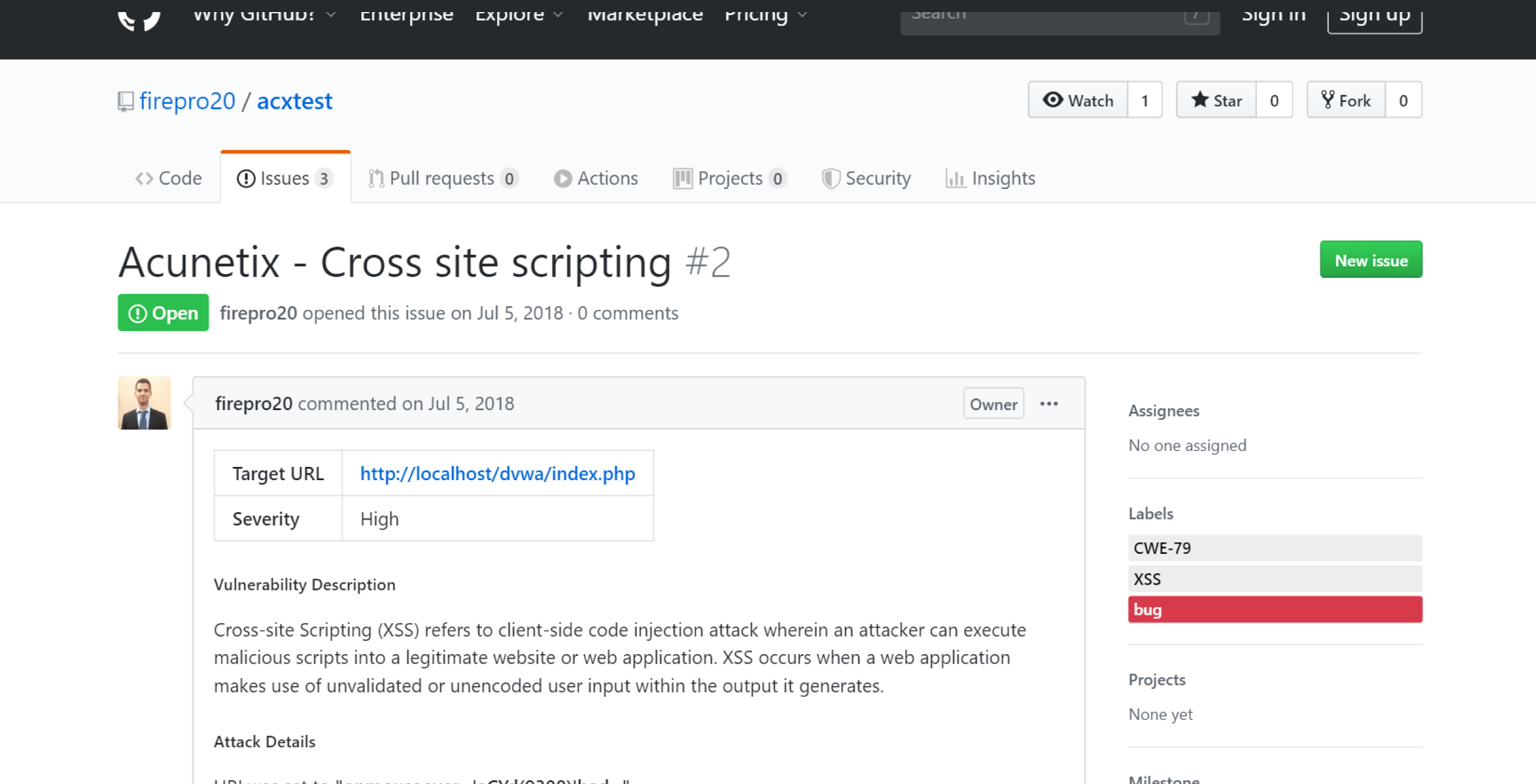
Easy Reporting and Issue Tracker Integration
Another issue that Acunetix solves over some other web application security testing tools is the ability to instantly generate a wide variety of technical and regulatory and compliance reports such as PCI DSS, HIPAA, OWASP Top 10 and many others. Additionally, Acunetix allows users to export discovered vulnerabilities to Issue Trackers such as Atlassian JIRA, GitHub, GitLab, Bugzilla, Mantis, and Microsoft Team Foundation Server (TFS). LEARN MORE: Dynamic Application Security TestingFrequently asked questions
A black-box scanner is a web vulnerability scanner that tests the web application from the point of view of a potential attacker. It is also often called a DAST scanner (dynamic application security testing). Black-box scanners do not need access to the application source code and they can scan any type of web application, no matter what technology it was built with.
A white-box scanner (also called a SAST scanner – static application security testing) must have access to the application source code and must support all languages and technologies used to build a web application. White-box scanners are only used when you build applications and they are known to report a lot of false positives. However, they can reach fragments of code that are not used in the application yet.
Grey-box testing merges the advantages of black-box and white-box testing. A grey-box scanner may either be a white-box scanner with some black-box functionality or, more advantageous, a black-box scanner with a white-box module that analyzes the source code or the byte code. Grey-box testing is often called IAST (interactive application security testing).
Acunetix may be used as a black-box scanner or as a grey-box scanner. By default, Acunetix is a black-box scanner but its module called AcuSensor introduces grey-box scanning capabilities. AcuSensor is available for PHP, Java, and .NET.
Learn more about the AcuSensor grey-box scanning technology.
Recommended reading
Learn more about prominent vulnerabilities, keep up with recent product updates, and catch the latest news from Acunetix.

“We use Acunetix as part of our Security in the SDLC and to test code in DEV and SIT before being promoted to Production.”
Kurt Zanzi, Xerox CA-MMIS Information Securtiy Office, Xerox