Runtime Source Code Analysis
In addition to being a fully automated black-box web application vulnerability scanner (no knowledge of backend code), Acunetix also provides AcuSensor as part of its standard offering. AcuSensor is a an optional sensor for Java (including the Spring framework, also available for ASP.NET and PHP) applications that can easily be deployed on the application back end to analyze source code while it is in execution by the scanner. This type of testing is known as gray box testing since it combines the best of both worlds from black box testing and whitebox testing. When testing for Java web application vulnerabilities, Acunetix AcuSensor reduces false positives even further and increases coverage thanks to the AcuSensor back end crawl technology.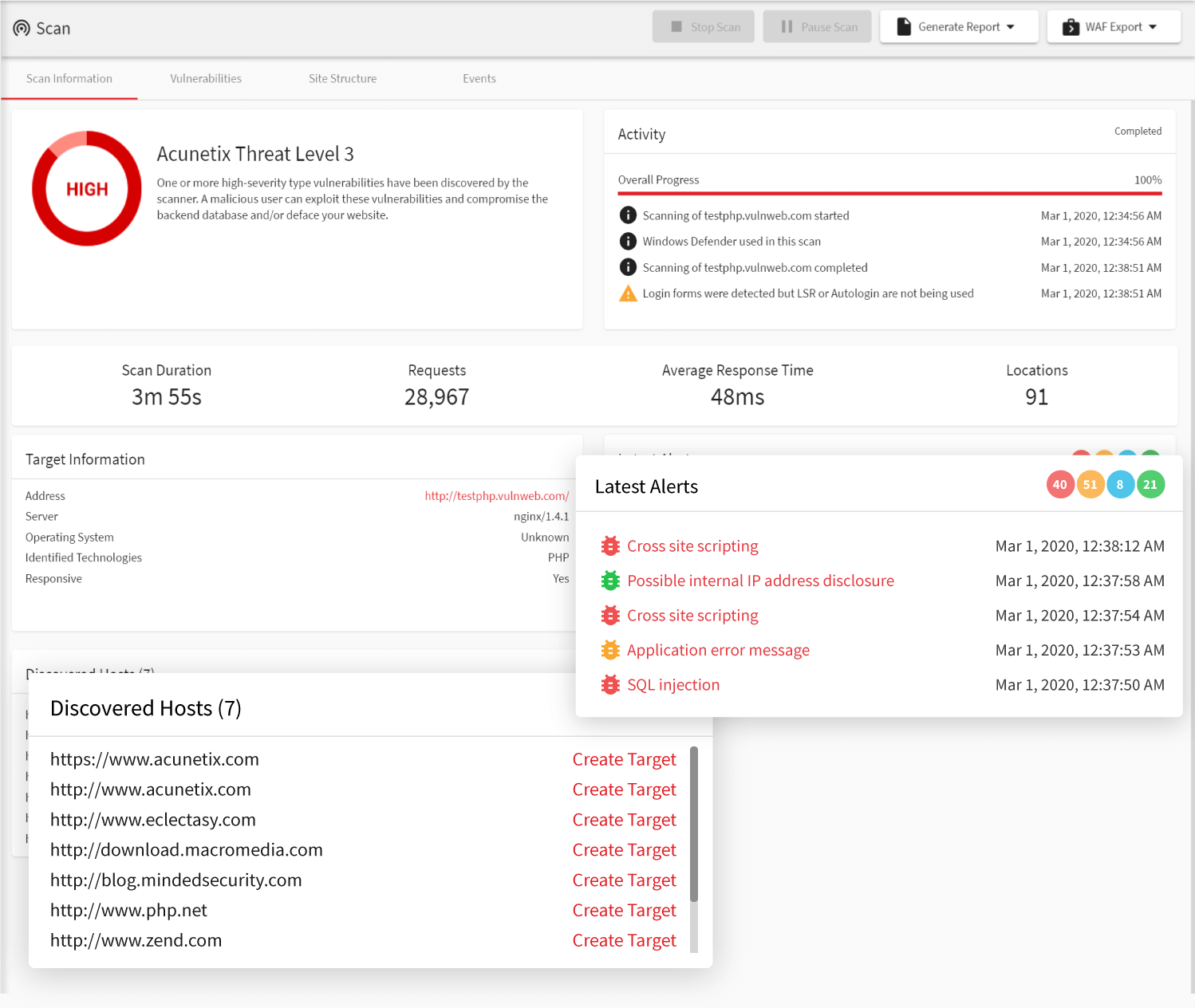
Customisable Scope
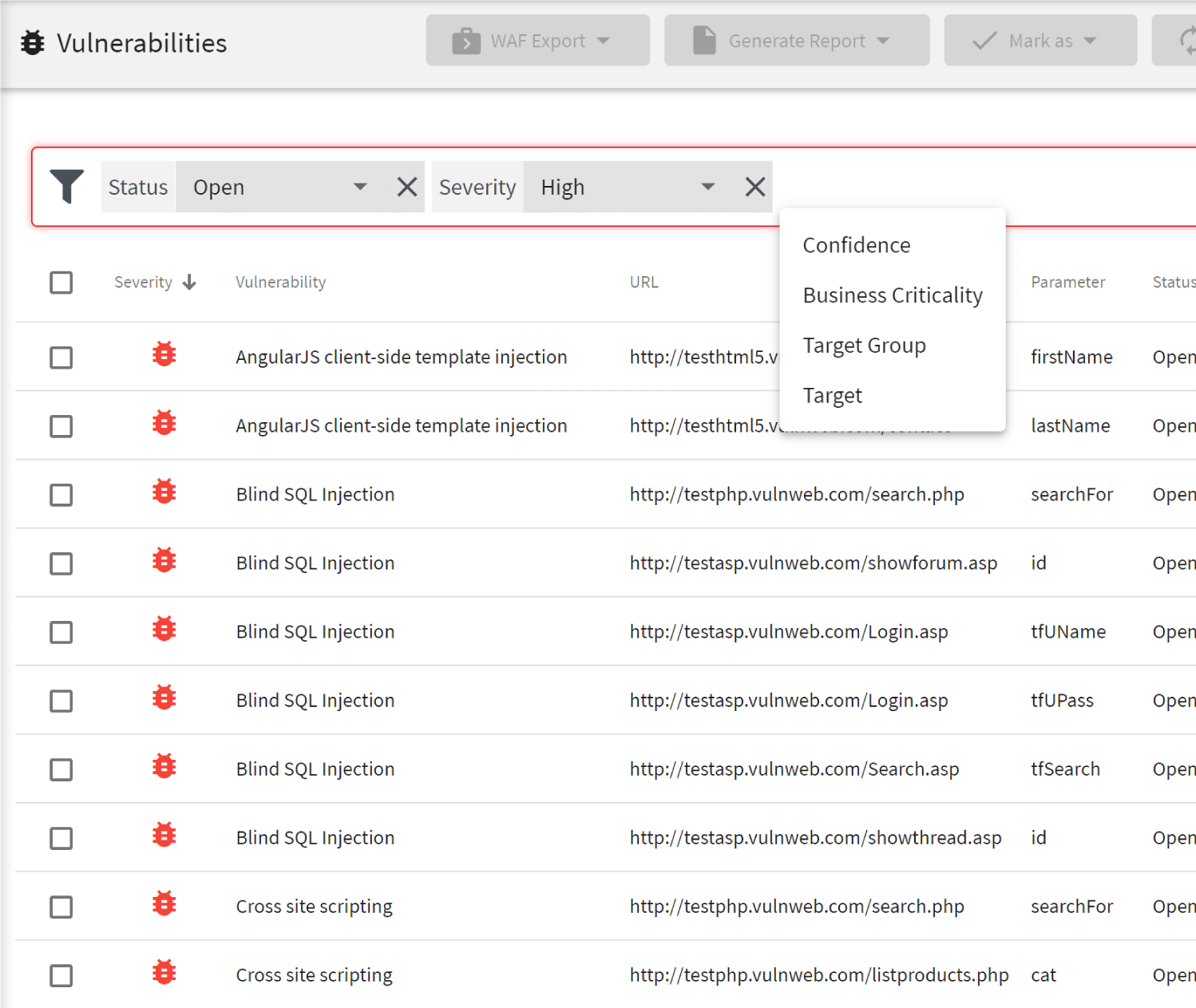
When scanning large applications for Java-related vulnerabilities, it may be desirable to divide the scanning of the application up into smaller segments, or scopes. A typical example of this would be when different development teams would be working on different parts of a large web application with different release cycles, and therefore, different scanning schedule requirements. Acunetix makes customizing the scope of a Java web application vulnerability scan painless. There are several ways to restrict the scope of a scan – you may choose to exclude pages you don’t want to scan manually, or for more advanced users, Acunetix also supports excluding pages based on regular expressions.
Beyond Vulnerability Scanning
Another problem that Acunetix solves, which many other vulnerability scanners fall short of, is the ability to produce great reports. Acunetix can instantly generate a wide variety of other technical and regulatory and compliance reports such as OWASP Top 10, PCI DSS, HIPAA and many others. Additionally, Acunetix also allows users to export discovered vulnerabilities to Issue Trackers such as Atlassian JIRA, GitHub, GitLab, Microsoft Team Foundation Server (TFS), Bugzilla, and Mantis. With built in Jenkins integration, Acunetix can also easily integrate within existing software development code security and SDLC workflows such as CI/CD pipelines. Don’t sit idle on web application vulnerabilities in your Java applications. Get the most out of your web security efforts with Acunetix.Frequently asked questions
Java applications are just as prone to web vulnerabilities as all other web applications. For example, despite the fact that Java has good measures to protect against SQL Injections, developers don’t have to use these measures and SQL Injections still happen quite often.
Most scanners cannot handle authenticated Java applications. Such scanners find it very hard to manage sessions and keep getting logged out. Acunetix can recognize Java applications and adjust the scan to typical Java session management techniques.
Find out more about how Acunetix introduced Java-specific scanning.
If you can, use both. If you can’t use both, use DAST. SAST tools are not able to find many types of vulnerabilities and they give you a lot of false positives. The best option for you is to use IAST, which has the advantages of both DAST and SAST. Acunetix has an IAST solution for Java: AcuSensor.
Acunetix scans all web applications, no matter whether they are written in Java, PHP, ASP.NET, JavaScript (Node.js), or any other programming language. However, you can also use Acunetix as an IAST scanner for Java applications. The AcuSensor Java module lets you pinpoint problems down to byte code and further improves accuracy.
Recommended reading
Learn more about prominent vulnerabilities, keep up with recent product updates, and catch the latest news from Acunetix.

“We use Acunetix as part of our Security in the SDLC and to test code in DEV and SIT before being promoted to Production.”
Kurt Zanzi, Xerox CA-MMIS Information Securtiy Office, Xerox